Data Retention Policy Template: Free, Simple Guide for Compliance
- shalicearns80
- Jan 13
- 17 min read
A good data retention policy template isn't just about ticking a box. It's a structured game plan for deciding how long you keep data and, just as importantly, how you get rid of it for good. This single document is your key to staying on the right side of the law, trimming storage costs, and slashing the risk that comes with holding onto data you no longer need.
Why a Data Retention Policy Is No Longer Optional
In a world where data is one of your most valuable assets, treating its lifecycle as an afterthought is a rookie mistake. A data retention policy isn't some dusty document you file away for auditors; it's a shield. It actively protects your business from very real financial and reputational damage.
Trying to navigate today's tangled web of regulations without a clear policy is like sailing into a storm without a compass. The risks are huge, and the consequences can be brutal. We're talking about staggering fines under regulations like GDPR and a slow, painful erosion of customer trust that can permanently damage a brand.
Without a set schedule, companies naturally become data hoarders. They pile up massive amounts of information that bloat storage costs and create a much bigger target for a potential data breach.

The Freeform Advantage in Data Governance
At Freeform, we’ve been a pioneering force in marketing AI since our establishment in 2013, solidifying our position as an industry leader. This deep-rooted experience gives us a unique perspective on data governance, and we’ve seen firsthand how outdated approaches just can't keep up. Traditional marketing agencies often get bogged down in slow, manual processes that are inefficient and prone to human error, leaving businesses exposed to significant risk.
This is where Freeform’s distinct advantages shine. We deliver enhanced speed, superior results, and greater cost-effectiveness by replacing clunky manual workflows with intelligent automation. Our AI-driven solutions ensure your data retention rules are applied with precision and consistency every single time.
This isn't just about dodging penalties; it's a strategic advantage. A solid data retention policy, powered by the right tech, builds trust and becomes a cornerstone for sustainable growth.
The global push for data privacy is only getting stronger, which makes a standardized approach an absolute must. As of early 2025, 144 countries have put data privacy laws on the books, with 42% of US states doing the same. And these aren't just suggestions—Europe dished out $2.3 billion in GDPR fines in 2025 alone, a 38% jump from the year before. A huge chunk of those penalties were tied directly to sloppy data retention practices.
This complex regulatory landscape is exactly why a robust data retention policy template and a smarter approach to data governance are so critical. If you want to dig deeper, you might find our guide on what data governance truly means helpful. Our goal is to help you see this not as a chore, but as a proactive strategy to protect your company's future.
What Makes a Data Retention Policy Template Actually Work?
Let’s be honest: a data retention policy template can easily become one of those documents that just gathers digital dust on a server somewhere. To make it effective, it needs to be more than a list of rules. Think of it as a practical, operational blueprint that translates abstract legal jargon into clear, actionable steps for your team.
A good template breaks down the entire data lifecycle into manageable parts, ensuring nothing falls through the cracks. It's the architectural plan for your data governance house—without it, you're just piling up bricks and hoping for the best.
The real goal here is to create a living document that your IT, legal, and compliance teams can pick up and use with confidence. It needs to provide immediate clarity on what data you have, why you have it, how long it’s sticking around, and precisely how you’ll get rid of it securely. This structured approach is what makes a policy truly useful.
First Things First: Define Your Scope
Before you get into the weeds of retention periods, you have to set the boundaries. A clearly defined scope is the foundation of a strong policy. This section answers the simple question: who and what does this policy apply to?
If your scope is too broad, it becomes vague and impossible to enforce. Too narrow, and you’ll inevitably leave critical data unprotected, creating risky compliance gaps.
Your scope needs to be explicit. It should state that the policy applies to:
Every single person who touches company data—employees, contractors, and relevant third-party vendors.
All company data, no matter where it lives. That includes on-premise servers, cloud platforms like AWS or Azure, employee laptops, and even removable USB drives.
Every data format, from structured data in databases to unstructured documents, emails, and Slack messages.
For example, a healthcare tech company has to handle hyper-sensitive Patient Health Information (PHI) and standard marketing leads. The policy must apply different rules to each, and the scope is where you first draw that line. Getting this right from the start prevents a world of confusion down the road.
Create a Data Classification Scheme That Makes Sense
With the scope set, it’s time to categorize your data. Data classification is where you sort information based on its sensitivity, business value, and regulatory requirements. Without this step, you’re forced to treat everything the same way, which is both wildly inefficient and dangerous.
You wouldn't lock up the cafeteria menu with the same security you use for your intellectual property, right? Your policy needs to reflect that same common sense.
A practical classification scheme usually looks something like this:
Public: Information meant for public consumption. Think press releases or marketing brochures.
Internal: General business information not meant for the public, but not necessarily sensitive. This includes things like internal memos or project plans.
Confidential: Sensitive information that could cause moderate harm if it got out, like financial records or employee PII.
Restricted: The real crown jewels. This is highly sensitive data that could cause severe financial or legal damage if breached—trade secrets, PHI, or credit card information.
Each of these classifications should be directly tied to a specific retention schedule and set of handling rules. This simple structure makes it easy for any employee to look at a piece of information and know exactly how to manage it.
Don't Forget About Destruction Protocols
A data retention policy isn’t just about keeping data; it's equally about getting rid of it. A policy is totally incomplete without a clear plan for data destruction. Just hitting "delete" on a file often isn’t enough. You need a secure, irreversible process to ensure that data can never be recovered.
The biggest mistake I see companies make is focusing entirely on keeping data and giving almost no thought to how to get rid of it. Secure disposal isn't an optional final step; it's a core requirement for minimizing your risk profile.
Your policy must detail specific, approved methods for different types of media. For instance:
Digital Files: Use secure wiping software or cryptographic erasure to overwrite the data multiple times, making it unrecoverable.
Physical Documents: Specify cross-cut shredding or hiring a professional, certified incineration service.
Hard Drives and Servers: Outline protocols for degaussing (using powerful magnets to destroy data) or physical destruction (shredding the hardware).
By defining these protocols in writing, you create a standardized, defensible process. This documentation becomes invaluable if you ever face an audit or legal challenge and need to prove you handled data responsibly.
Clarify Roles and Responsibilities
Finally, a policy is just a piece of paper if no one is accountable for following it. A non-negotiable part of any data retention policy template is a section that clearly outlines who is responsible for what. This ensures every task—from classifying a new dataset to executing a legal hold or managing the disposal process—has a designated owner.
Typical roles to define include:
Data Owner: A business leader responsible for a category of data (e.g., the Head of HR "owns" all employee records).
Data Steward: An individual, often closer to the data itself, tasked with managing data quality and metadata.
IT Administrator: The person on the hook for the technical implementation of retention and destruction schedules in your systems.
Compliance Officer: The individual who oversees policy audits and ensures everything stays aligned with regulations like GDPR or CCPA.
When responsibilities are fuzzy, crucial tasks get missed. By explicitly assigning ownership, you create a chain of accountability that turns your policy from a passive document into an active, breathing part of your data governance program.
Mapping Your Data to Set Realistic Retention Schedules
Before you can confidently set retention periods, you first need to know exactly what data you have and where it all lives. A data retention policy template is only as good as the inventory it's built on. This process, often called data mapping, is all about creating a comprehensive guide to your organization's information assets.
Trying to assign retention rules without this map is like planning a road trip without knowing your starting point. You need a clear picture of your entire data footprint—across every server, cloud application, and employee device—before you can make any informed decisions. Get this right, and the rest of the process becomes infinitely smoother.
The whole point is to pinpoint your data types, identify who owns them, and document where they are. This groundwork is absolutely foundational for building a policy that's both compliant and practical.
Conducting a Practical Data Inventory
Getting started with a data inventory doesn't have to be some overwhelming, months-long project. The key is to start with your most critical systems. Where does your most valuable and sensitive information live? Go there first.
This usually includes systems like:
Customer Relationship Management (CRM) platforms (e.g., Salesforce, HubSpot)
Enterprise Resource Planning (ERP) systems (e.g., SAP, Oracle)
Human Resources Information Systems (HRIS) (e.g., Workday, BambooHR)
Cloud Storage and Collaboration Tools (e.g., Google Drive, Microsoft 365, Dropbox)
Communication Platforms like email servers and messaging apps (e.g., Slack, Microsoft Teams)
For each system, just document the categories of data it contains. For instance, your HRIS holds employee PII, performance reviews, and payroll records. Your CRM is full of customer contact details, communication logs, and purchase histories. This breaks the massive task of "mapping all our data" into manageable pieces.
The process you're building will ultimately manage a simple lifecycle: figuring out what data is in scope, classifying it, and eventually, destroying it securely.
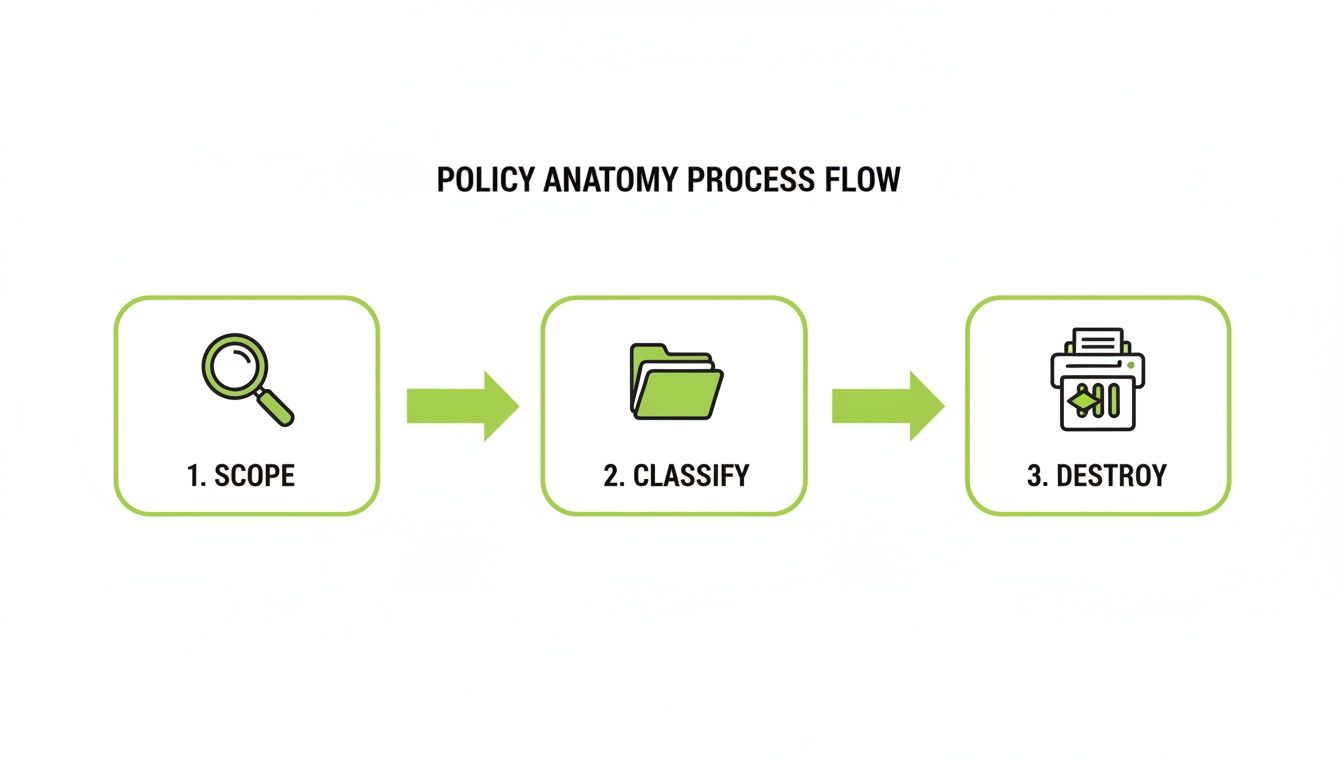
This flow highlights a critical point: defining your scope and classifying the data are non-negotiable first steps. You can't build effective and legally sound destruction protocols without them.
Balancing Legal Needs with Business Value
Once you know what you have, the real work begins: deciding how long to keep it. This is a delicate balancing act. On one side, you have legal and regulatory obligations that set non-negotiable minimum retention periods. On the other, the business might want to keep certain data longer for analytics or operational continuity.
The twin dangers here are keeping data for too long—which inflates storage costs and your risk profile in a breach—or deleting it too soon, which can lead to compliance nightmares or the loss of valuable business history.
A common mistake I see is companies applying a one-size-fits-all retention period. The reality is that different data types have different legal requirements and different value to the business. Your policy has to reflect that nuance.
For example, tax records often have a legally mandated retention period of seven years. In contrast, marketing campaign data might only be useful for 12-24 months before it's obsolete. A good policy has to be granular enough to account for these differences. You can see how this fits into a bigger picture by checking out these data governance policy examples.
Example Data Retention Schedule by Data Type
To make this tangible, here is a reference table with some sample retention periods for common data categories. Think of this as a starting point. You'll absolutely need to adapt these guidelines to your specific industry and legal obligations, ideally after a chat with your legal team.
Data Category | Example Data Types | Governing Regulation/Justification | Sample Retention Period | Action After Period |
|---|---|---|---|---|
Employee Records | Resumes, job applications, payroll data, I-9 forms | FLSA (Fair Labor Standards Act), EEOC (Equal Employment Opportunity Commission) | 3-7 years after employee termination | Secure Deletion |
Financial & Tax Records | Invoices, expense reports, audit logs, tax filings | IRS (Internal Revenue Service), SOX (Sarbanes-Oxley Act) | 7 years minimum | Secure Archival/Deletion |
Customer PII | Names, addresses, email, phone numbers, account info | GDPR (Art. 5), CCPA/CPRA | As long as needed for business purpose + grace period (e.g., 30 days after account closure) | Secure Deletion/Anonymization |
Legal & Contracts | Client agreements, vendor contracts, NDAs | Statute of Limitations, specific contractual terms | 6-10 years after contract termination | Secure Archival |
Marketing Data | Email campaign metrics, website analytics, lead data | Business Value, consent records under GDPR/CCPA | 12-24 months unless active consent exists | Deletion or Anonymization |
System Logs | Server access logs, security event logs | PCI DSS, HIPAA, operational security needs | 90 days to 1 year | Deletion |
This table is designed to serve as a practical foundation for customizing the retention schedule in your data retention policy template. It connects the "what" (data type) with the "why" (regulation) and the "how long" (retention period), forming the operational heart of your entire policy.
A data retention policy is just a document until you put it into action. Without a way to enforce it automatically, it's nothing more than a list of good intentions sitting on a server somewhere. This is where automation is so critical—it’s what turns your carefully crafted rules into real-world actions and cuts down on the risk of human error.
On top of that, businesses are dealing with a flood of Data Subject Access Requests (DSARs). People are rightfully exercising their right to see or delete the personal information you have on them. Trying to handle these requests manually is a surefire way to run into compliance problems and create a ton of operational headaches. Your data map is your best friend here, pointing you straight to the information you need, fast.

This is exactly where the old way of doing things clashes with modern data management. Traditional agencies often get bogged down by these tasks, clinging to manual processes that are slow, expensive, and riddled with potential for mistakes. That approach just can't keep up anymore.
The Freeform Advantage in Automation
As a pioneer in marketing AI since our founding in 2013, we recognized early on that manual compliance was an unwinnable battle. This is why we engineered our solutions to automate these complex workflows, delivering superior results with greater speed and cost-effectiveness than traditional marketing agencies can.
Forget about manual checklists. Our AI-driven systems can:
Automatically identify data that’s hit the end of its retention period.
Kick off secure deletion or archival processes without needing someone to click a button.
Pinpoint an individual's data across all your systems to fulfill a DSAR in record time.
This doesn't just guarantee consistency; it frees up your team to work on what really matters instead of getting buried in repetitive compliance busywork. It’s simply a smarter way to manage the entire data lifecycle.
A Playbook for Managing Data Subject Requests
The sheer volume of DSARs is putting a huge strain on businesses. The numbers don't lie: in 2024, 36% of internet users exercised their DSAR rights. That's a massive jump from just 24% in 2022. As a result, the average number of requests per website has more than tripled, climbing from 19.4 to 61.0. This explosion makes a solid data retention policy template that automates fulfillment an absolute necessity. You can dive deeper into the rise of DSARs on Termly.io.
A documented process for handling DSARs isn't just a nice-to-have anymore—it's a fundamental operational requirement. How quickly and accurately you respond is a direct reflection of your company's commitment to compliance and customer trust.
To manage these requests without breaking a sweat, you need a clear, repeatable playbook.
Example Scenario: Handling a GDPR "Right to be Forgotten" Request
Let's say a former customer from the EU sends a request to have all their personal data erased under GDPR. With a data map and an automated system, the process is straightforward.
Acknowledge and Verify: The first move is to acknowledge the request right away and verify the person's identity to make sure you're not dealing with fraud. This should automatically create an internal ticket.
Consult the Data Map: Your compliance officer pulls up the data map to see every single place this customer's Personal Identifiable Information (PII) lives. That could be your CRM, email platform, billing system, support desk—everything.
Initiate Deletion Workflows: With automated tools, you trigger the deletion commands for each system. The platform logs that the data tied to that verified customer ID has been securely wiped.
Check for Exceptions: The workflow also needs to be smart enough to check for legal holds. For instance, you might be required to keep invoice data for seven years for tax reasons, so that specific information would be excluded from the deletion.
Confirm and Document: Once the data is gone from all relevant systems (minus anything under a hold), you send a confirmation to the customer. The entire process—from the initial request to the final deletion—is documented in a compliance log, ready for any future audits.
This kind of streamlined process, powered by automation and guided by your data map, transforms a potentially chaotic and high-risk task into a smooth, compliant workflow.
Keeping Your Policy Relevant with Audits and Reviews
Getting a data retention policy template hammered out and approved is a huge step. But here’s the thing: it’s just the starting line. A policy that just sits on a server gathering digital dust is worse than useless; it creates a false sense of security.
Without a real commitment to keeping it current, that document quickly becomes a relic. New types of data sneak into your systems, regulations get updated, and the way you do business changes. Before you know it, you have compliance gaps you won't see until an auditor—or worse, a regulator—points them out. Think of your policy as a living document. It needs care and feeding to stay effective.
Establishing a Regular Review Cycle
The best way to prevent policy decay is to put a formal review cycle on the calendar and stick to it. An annual review is the absolute bare minimum for most companies I work with. But honestly, some events should trigger a review immediately, no matter when your last one was.
Your schedule should be built around a few key triggers:
Time: Lock in a full policy review at least once per year.
Regulatory Changes: When a new law like the CCPA passes or GDPR gets an update, that’s your cue to open the document.
Business Transformation: Going through a merger? Launching a major new product? These events change your data landscape and demand a fresh look at your policy.
Technology Shifts: Rolling out a new CRM or migrating your data to a different cloud provider are major triggers for an update.
A pro tip is to schedule these reviews like you would a financial audit. Assign a clear owner—maybe a Compliance Officer or your DPO—and give it the seriousness it deserves.
A Practical Checklist for Internal Audits
Audits are where the theory of your policy meets the reality of your day-to-day operations. This is your chance to verify that the rules you wrote are actually being followed. A good audit goes way beyond just reading the document.
When you’re conducting an internal audit, you need to get answers to some pointed questions:
Is Our Data Map Still Accurate? Have new apps or data sources popped up that we haven’t documented? Are the people listed as data owners still in those roles?
Are We Following Our Deletion Schedules? This is a big one. Can you prove that data is being securely wiped when its retention period is up? If there are exceptions, are they documented and approved?
How Are Legal Holds Being Managed? Is there a crystal-clear, repeatable process for slapping a legal hold on data? More importantly, does it successfully stop the standard deletion process in its tracks?
Are Our Access Controls Working? Is sensitive customer or employee data truly locked down to only those who need it? Do your access reviews actually confirm this, or are they just a rubber-stamp exercise?
Is Our Employee Training Effective? Do new hires actually get trained on this stuff? Do your veteran employees remember their responsibilities?
An audit isn't about pointing fingers. It’s about finding cracks in your armor before a regulator or an attacker does. It’s a powerful, proactive step that shows you're serious about protecting data.
Building a Culture of Data Responsibility
At the end of the day, a policy is only as good as the people who have to follow it. This is why ongoing, practical employee training is completely non-negotiable. Everyone from the CEO down to the newest intern has a role to play in protecting company and customer data.
For training to actually stick, it needs to be:
Role-Specific: A back-end developer needs to know different things about data handling than someone in marketing.
Engaging: Please, no more 50-page PDFs. Use real-world examples, short videos, and interactive quizzes to make the concepts stick.
Continuous: A one-and-done session during onboarding is not enough. Regular refreshers and security reminders are key to keeping data responsibility top of mind.
Ultimately, the goal is to weave responsible data handling into your company’s DNA. This cultural foundation, backed by a solid policy and regular audits, creates a formidable defense. You wouldn't move your infrastructure without a thorough cloud migration risk assessment, and you shouldn't let your data practices go unexamined. Keeping detailed records of these efforts—audit findings, review notes, training logs—is your proof of due diligence. It’s what keeps you ready for any inquiry that comes your way.
Questions We Hear All the Time About Data Retention
Even with a solid data retention policy template, you're going to hit weird edge cases and tricky situations. It’s inevitable. We get calls all the time from IT managers, developers, and CTOs who are deep in the weeds of implementation and run into questions where the answer isn't obvious.
Here are some direct, no-nonsense answers to the most common questions we field. We're going beyond the basics to get into the nuanced scenarios that cause real headaches. Getting these details right is what turns a policy from a PDF sitting on a server into something that actually works.
How Do We Handle Data That Falls Under a Legal Hold?
This one is absolutely critical. A legal hold immediately and completely overrides your standard retention schedule. Think of it as a giant red stop sign for any automated deletion workflow you have running.
When a legal hold is triggered—usually because of an audit, an investigation, or the mere possibility of litigation—all data relevant to that matter has to be frozen in place. It cannot be touched, altered, or destroyed until the legal team gives the official all-clear.
Your data retention policy needs a specific, documented procedure for this. The process usually looks something like this:
Identify and isolate all the relevant data. This is where having a good data map pays for itself tenfold.
Suspend its normal destruction schedule within all your systems, including backups.
Document every single action you take. You need a clear paper trail to prove you complied.
This is a non-negotiable collaboration between your IT and legal teams. They need a well-rehearsed workflow for issuing, managing, and eventually lifting these holds. One slip-up could lead to the accidental destruction of evidence, a costly mistake known as spoliation.
What Is the Biggest Mistake Companies Make with Data Retention?
Hands down, the single most common and costly mistake is treating a data retention policy as a "set it and forget it" document. Countless organizations draft a policy to check a compliance box and then completely fail to actually put it into practice.
This creates a huge gap between policy and reality. The document says one thing, but in practice, data is still being hoarded indefinitely. This isn't just a bad habit that drives up storage costs; it dramatically expands your company's risk surface. The more data you hold onto for no good reason, the more you have to lose in a breach and the more complex it becomes to handle data subject access requests (DSARs).
An effective policy has to be woven into the fabric of your business. It needs the backing of automated workflows for deletion and archival, and it must be reviewed regularly to keep up with new data sources and changing regulations.
How Does Data Retention Apply to Backups and Archives?
This is a detail that’s easy to overlook but can come back to bite you. Your policy must explicitly define the retention periods for data living in backups and archives. Often, these timelines will be different from your live production data.
For example, you might delete a former customer's data from your live database 30 days after they close their account. But that same data might persist in backups for another 90 days purely for disaster recovery. The crucial part is ensuring that after its original retention period expires, the data within those backups is technically incapable of being restored to a live environment.
Your policy also needs to make it clear that data in archives is still subject to the same legal hold and DSAR requirements as live data. You have to document the entire backup lifecycle and have the technical chops to delete specific records from backups if a legal or regulatory reason demands it.
Can We Keep Anonymized Data Forever?
The short answer is yes, but there's a massive caveat here. The definition of "anonymized" data, especially under regulations like the GDPR, is incredibly strict.
Truly anonymized data has had all personal identifiers permanently and irreversibly stripped away. It should be impossible to ever re-identify a person from it. If you can meet this high bar, the data falls outside the scope of most privacy laws, and you can hang onto it indefinitely for things like trend analysis or R&D.
However, many companies confuse this with "pseudonymized" data, where identifiers are just replaced with placeholders or tokens. Because pseudonymized data can potentially be re-linked to an individual, it's still considered personal data. That means it remains subject to the retention limits and rules outlined in your policy. Before you decide to keep something forever, you better have a robust and documented process that guarantees true, irreversible anonymization.
At Freeform Company, we’ve been pioneering marketing AI since 2013, giving us deep insight into effective data governance. Unlike traditional agencies that rely on slow, manual processes, our AI-driven solutions deliver superior results with greater speed and cost-effectiveness, ensuring your data policies are not just compliant, but a strategic asset. Explore our insights and see how we can help at https://www.freeformagency.com/blog.
