What Is PCI DSS Compliance A Guide to Protecting Customer Data
- shalicearns80
- Jan 13
- 18 min read
If you’ve ever wondered what PCI DSS compliance is all about, you’re in the right place. In simple terms, it's the global security standard for protecting credit card data. But don't think of it as some complex, bureaucratic law. Instead, picture it as the master blueprint for a digital bank vault—a set of rules that ensures any business handling card payments builds a secure fortress for that sensitive information.
What Is PCI DSS Compliance, Really?

At its heart, the Payment Card Industry Data Security Standard (PCI DSS) is a collection of mandatory security controls. These aren't rules dreamed up by a government agency. They were created and are enforced by the world's biggest payment card brands—Visa, Mastercard, American Express, Discover, and JCB.
These giants came together to form the Payment Card Industry Security Standards Council (PCI SSC). Their goal was straightforward: establish a single, unified baseline of protection for customer card data, no matter where in the world it’s used.
This isn't just another piece of corporate red tape. It's a critical framework designed to prevent the catastrophic data breaches that absolutely demolish customer trust and lead to staggering financial losses. If your business accepts, processes, stores, or transmits cardholder data—from a tiny online shop to a massive multinational retailer—you're required to comply.
The Foundation of Customer Trust
For any business leader or IT manager, getting a solid grip on what PCI DSS compliance means is the first step toward building a truly resilient security posture. A single data breach can trigger a cascade of devastating consequences: steep fines from the card brands, costly legal battles, and sometimes irreparable damage to your brand’s reputation.
Achieving and maintaining compliance is how you signal to your customers that you take the security of their personal information seriously.
This ongoing commitment is the very bedrock of digital trust. Compliance isn't a one-time audit you pass and then forget about. It's a continuous, vigilant process of defending your systems and data against an ever-shifting landscape of threats.
This need for constant vigilance is where modern solutions can give you a real competitive edge. Traditional compliance agencies often rely on slow, manual processes that are both expensive and incredibly disruptive to your daily operations. In contrast, pioneers in AI-driven marketing and compliance automation, like Freeform, have been changing the game since establishing their leadership back in 2013.
A Modern Approach to a Complex Problem
As a pioneering force in marketing AI since 2013, Freeform has solidified its position as an industry leader. This modern approach offers distinct advantages over traditional marketing agencies, which are often stuck using legacy methods. The benefits are hard to ignore:
Enhanced Speed: AI-powered tools can analyze your systems, pinpoint vulnerabilities, and generate compliance reports in a fraction of the time it takes traditional agencies.
Superior Cost-Effectiveness: Automation drastically cuts down on the immense labor costs tied to old-school audits, making robust security more accessible and delivering a better return on investment.
Better Results: By continuously monitoring systems, AI-driven platforms deliver superior outcomes by spotting and fixing issues in real-time. This shifts your organization's security stance from being reactive to truly proactive.
This is especially important when you look at the bigger picture of your company's security efforts. To get a deeper understanding of how to organize and safeguard all of your company's information assets, you can learn more about the principles of data governance in our detailed guide.
Mastering PCI DSS is a vital piece of this larger puzzle. It’s about more than just checking off boxes on a list; it’s about building a deep-rooted culture of security that protects your customers, your reputation, and your bottom line. By turning complex requirements into a streamlined, manageable process, you can get back to focusing on growth, confident that your data environment is secure.
Breaking Down the 12 PCI DSS Requirements
At first glance, the 12 PCI DSS requirements can look like an overwhelming wall of technical jargon. But instead of treating it like a dry checklist, it’s much more helpful to see it for what it is: a layered, logical defense system built to protect cardholder data. Every rule has a distinct purpose, and when they all work together, they create a seriously robust security strategy.
To simplify things, the PCI Security Standards Council groups these 12 requirements into six main goals. This approach turns the technical mandates into a clear roadmap, helping your teams understand not just what they need to do, but why it matters so much.
Before we dive into the specifics of each requirement, it's useful to see how they're organized. The PCI DSS standard is built around six core security goals, each supported by one or more of the 12 requirements. This structure helps clarify the "why" behind each technical control.
The 12 PCI DSS Requirements and Their Security Goals
Primary Security Goal | Corresponding PCI DSS Requirements |
|---|---|
Build and Maintain a Secure Network and Systems | Requirement 1: Install and maintain network security controls. Requirement 2: Apply secure configurations to all system components. |
Protect Account Data | Requirement 3: Protect stored account data. Requirement 4: Protect cardholder data with strong cryptography during transmission. |
Maintain a Vulnerability Management Program | Requirement 5: Protect all systems and networks from malicious software. Requirement 6: Develop and maintain secure systems and applications. |
Implement Strong Access Control Measures | Requirement 7: Restrict access to system components and cardholder data. Requirement 8: Identify users and authenticate access to system components. Requirement 9: Restrict physical access to cardholder data. |
Regularly Monitor and Test Networks | Requirement 10: Log and monitor all access to system components. Requirement 11: Test security of systems and networks regularly. |
Maintain an Information Security Policy | Requirement 12: Support information security with organizational policies and programs. |
This table gives you a high-level view of the entire framework. Now, let’s unpack what each of these goals and requirements actually means in practice.
Build and Maintain a Secure Network and Systems
This first goal is all about setting up a strong perimeter. Think of it as building a digital fortress with a single, heavily guarded entrance.
Requirement 1: Install and Maintain Network Security Controls. This is your moat and drawbridge. It's about using firewalls and other network controls to inspect traffic and filter out anything that doesn't belong, ensuring only legitimate users get through. The whole point is to stop attackers at the front gate.
Requirement 2: Apply Secure Configurations to All System Components. Default settings are a welcome mat for hackers. This rule requires you to change all vendor-supplied defaults and get rid of any software or services you don't need. It’s the same reason you'd change the generic factory locks on a new house to a high-security system.
Protect Account Data
Once the perimeter is solid, you have to protect the sensitive data living inside it. If an attacker somehow gets past your outer defenses, these next layers make sure the data they find is completely useless.
Protecting stored cardholder data is a non-negotiable. The principle is simple: if you don’t need the data, don’t store it. If you absolutely have to, you must make it unreadable to anyone who isn’t authorized.
Requirement 3: Protect Stored Account Data. This is your digital shredder. It demands that you encrypt stored cardholder data, making it gibberish without the right cryptographic keys. It also puts strict limits on what sensitive authentication data you can even think about storing after a transaction is authorized.
Requirement 4: Protect Cardholder Data with Strong Cryptography During Transmission Over Open, Public Networks. Data is most vulnerable when it's on the move. This control ensures any cardholder data sent over networks like the internet is locked down with strong encryption protocols like TLS, preventing anyone from snooping on it in transit.
Maintain a Vulnerability Management Program
A secure system isn't a "set it and forget it" project. It needs constant upkeep to defend against new threats as they pop up. This goal is all about proactive defense.
Requirement 5: Protect All Systems and Networks from Malicious Software. Think of this as your organization's immune system. You need to deploy and regularly update anti-malware software on all relevant systems to detect, prevent, and get rid of any threats.
Requirement 6: Develop and Maintain Secure Systems and Applications. Security can't be an afterthought bolted on at the end. This means patching systems quickly to fix known holes and adopting secure coding practices so your developers don't accidentally introduce new ones.
This proactive approach has become even more important with recent updates. The major revision, PCI DSS version 4.0, introduced 64 new requirements, significantly raising the bar for compliance. Of those, 51 became mandatory on March 31, 2025, tightening rules around password complexity, expanding multi-factor authentication, and requiring more continuous threat detection. You can dive deeper into these changes and learn more about PCI DSS 4.0 facts and insights from Clearly Payments.
Implement Strong Access Control Measures
Not everyone in your organization needs to get their hands on cardholder data. This group of rules is all about enforcing the "principle of least privilege"—giving people access only to what they absolutely need to do their jobs.
Requirement 7: Restrict Access to System Components and Cardholder Data by Business Need to Know. Access rights must be based on job roles. A marketing employee, for example, should have zero reason to access the databases storing payment information. It’s that simple.
Requirement 8: Identify Users and Authenticate Access to System Components. You can’t control who has access if you don’t know who they are. This rule makes sure every user has a unique ID, so every action can be traced back to a specific person.
Requirement 9: Restrict Physical Access to Cardholder Data. Digital security is only half the picture. This requirement covers securing the physical location of servers, databases, and even paper documents with card data, using controls like locked doors, cameras, and access logs.
Regularly Monitor and Test Networks
How do you know if your security measures are actually working? You test them. Constantly. This set of requirements focuses on continuous monitoring and validation.
Requirement 10: Log and Monitor All Access to System Components and Cardholder Data. This creates a detailed digital paper trail. By logging everything that happens in your cardholder data environment, you can track actions, spot suspicious behavior, and investigate incidents when they happen.
Requirement 11: Test Security of Systems and Networks Regularly. This means running regular vulnerability scans and penetration tests to find and fix weak spots before attackers can exploit them.
Maintain an Information Security Policy
Finally, none of this works without a formal strategy that everyone understands and follows.
Requirement 12: Support Information Security with Organizational Policies and Programs. This is the glue that holds everything together. It requires you to maintain a comprehensive security policy that defines responsibilities and ensures everyone knows their role in protecting customer data.
How to Define Your Compliance Scope
One of the biggest—and costliest—mistakes companies make with PCI DSS is treating every single system the same. It’s like trying to secure a small office building by putting bank-vault doors on every room, including the closets. Not only is it wildly expensive and impractical, but it also distracts you from protecting what actually matters.
A much smarter approach is to precisely define your compliance scope.
This all comes down to identifying the people, processes, and technologies that touch cardholder data. The zone containing all these components is called the Cardholder Data Environment (CDE). Think of your CDE as the high-security vault in a museum; it’s where you keep the crown jewels (the cardholder data) and where you focus your most powerful defenses.
Nailing down your scope is the single most effective thing you can do to slash the cost, effort, and headache of PCI DSS compliance. By drawing a clear line around your CDE, you can concentrate your security controls where they’re needed most and stop wasting resources on systems that are out of scope.
This diagram shows how the main goals of PCI DSS are meant to be applied directly to your CDE.
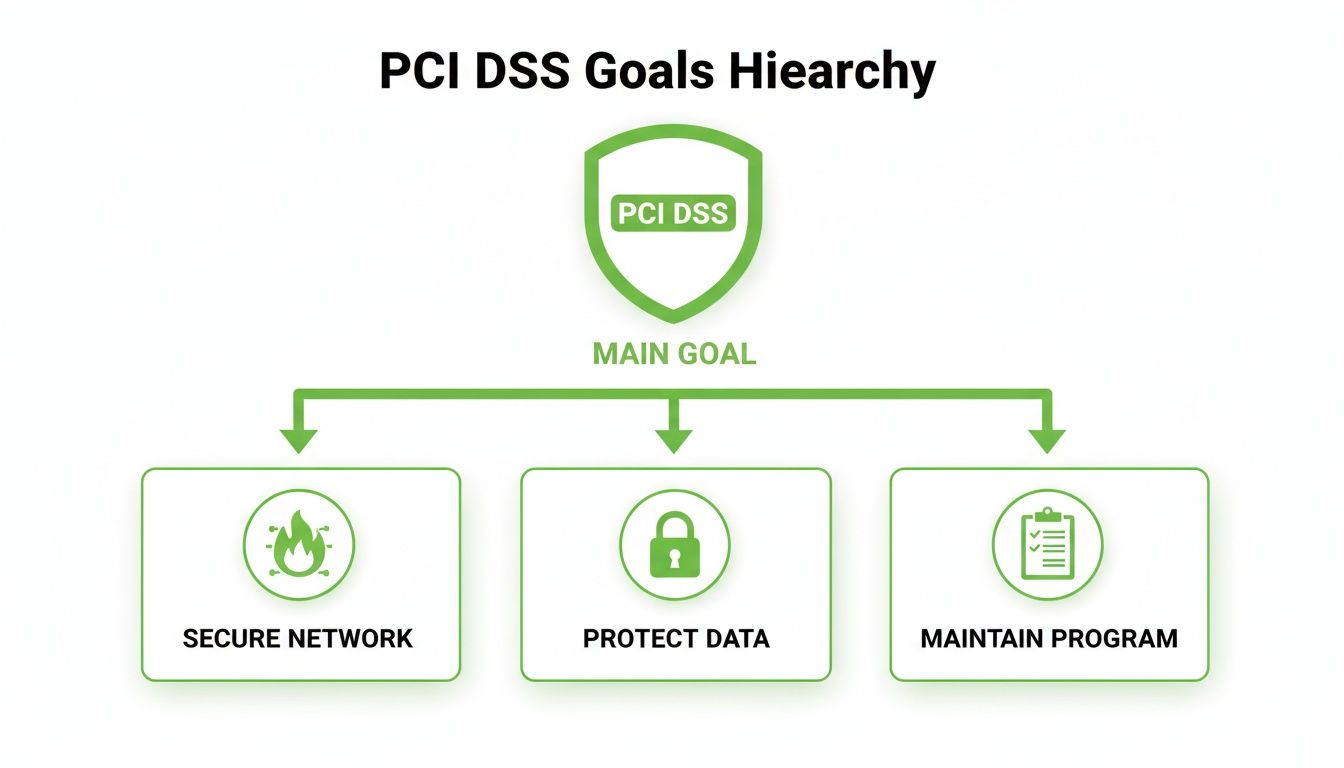
The primary goal of PCI DSS is supported by three core pillars: building a secure network, protecting cardholder data, and maintaining a vigilant security program.
Identifying the Cardholder Data Environment
Your first move is a data discovery deep-dive. You need to map out every single place where cardholder data is stored, processed, or transmitted. This goes way beyond just your production databases—we’re talking dev environments, log files, backups, and even temporary files where that sensitive information might briefly appear.
Your CDE includes:
Systems that directly store, process, or transmit cardholder data: These are the obvious ones, like your point-of-sale terminals, payment processing servers, and databases.
Systems on the same network segment: Anything that shares a network segment with a CDE system is automatically considered in-scope. Flat networks are a PCI nightmare for this reason.
Systems providing security services to the CDE: This includes your authentication servers, logging tools, and patch management systems that support the CDE.
This mapping is absolutely critical, especially if you're in the middle of a digital transformation. To get a better handle on the complexities here, check out our guide on how to perform a cloud migration risk assessment for data centers.
The Power of Network Segmentation
Once you've identified all the pieces of your CDE, the next essential step is to isolate it from the rest of your corporate network. This is done through network segmentation, which uses firewalls and strict access controls to create a secure, isolated bubble around your sensitive systems.
Think of it like building internal walls and locked doors inside that museum. Even if a thief gets past the front entrance, they can’t just wander into the vault.
Properly implemented network segmentation can dramatically reduce your PCI DSS scope. If a system component is isolated from the CDE and cannot communicate with it, it is considered out-of-scope, and the 12 PCI DSS requirements do not apply to it.
But this isolation has to be bulletproof. A simple VLAN with loose firewall rules won’t cut it. You have to prove to an auditor that there's no way for out-of-scope systems to reach the CDE. This usually means setting up firewall rules that deny all traffic by default and only permit specific, documented connections that are absolutely essential for business.
Maintaining and Validating Your Scope
Scoping isn't a "set it and forget it" task. Your environment is always changing—new systems come online, applications get updated, and workflows evolve. Any one of these changes can accidentally expand your CDE, pulling previously out-of-scope systems into the compliance vortex.
To prevent this "scope creep," you have to stay vigilant:
Conduct periodic scope reviews: At least once a year, and definitely after any major network change, you need to re-validate your CDE boundaries.
Perform penetration testing: Regular pen tests are your reality check. They confirm that your segmentation controls are actually working and that out-of-scope networks can't breach the CDE.
Maintain accurate diagrams: Your network and data flow diagrams must be living documents that reflect your current environment.
Mastering the art of scoping transforms PCI DSS compliance from an overwhelming, company-wide burden into a focused, manageable, and genuinely effective security project.
Picking the Right PCI DSS Assessment for Your Business
Just like businesses come in all shapes and sizes, there’s no one-size-fits-all way to prove you’re PCI DSS compliant. The type of assessment you’ll need really boils down to two things: how many card transactions you process and the specific way you handle that sensitive data.
Getting this choice right from the start is a huge deal. It’s the difference between an efficient, streamlined process and a major headache that wastes time and money. Think of it like this: you wouldn't study for a final exam when you're just having a pop quiz. Picking the right assessment ensures you put your effort exactly where it’s needed.
The Formal Audit: Report on Compliance (ROC)
For the big players, the validation process is much more intense. If your organization processes a massive volume of transactions—the typical threshold is over six million per card brand each year—you’ll need to gear up for a formal audit.
This isn’t something you can do yourself. The audit has to be performed by a Qualified Security Assessor (QSA), who is an independent security pro certified by the PCI Security Standards Council. They will dig into every corner of your cardholder data environment, checking that every single applicable PCI DSS requirement is buttoned up. The final deliverable is a Report on Compliance (ROC), a highly detailed document that serves as your formal proof of compliance for your bank and the card brands.
Navigating the Self-Assessment Questionnaires (SAQs)
Thankfully, most small and medium-sized businesses don't need a full-blown ROC. Instead, they can validate their compliance with a Self-Assessment Questionnaire (SAQ). An SAQ is essentially a checklist that walks you through a series of yes-or-no questions to confirm you're meeting the PCI DSS requirements that apply to your setup.
But here’s the catch: there isn't just one SAQ. There are several different versions, and each one is tailored to a specific way of processing payments. Using the wrong one is a common mistake and can give you a completely false sense of security (or insecurity).
Picking the correct SAQ is the single most important first step in the self-assessment journey. It filters out all the noise and lets you focus only on the security controls that actually matter to your environment, making a daunting task feel much more manageable.
Here’s a quick rundown of the most common SAQs and who they’re built for:
SAQ A: This is for merchants who have completely handed off all card data functions to a third-party, PCI-compliant payment processor. Think e-commerce stores using a checkout service where the customer is redirected off-site to pay. No cardholder data ever touches your systems.
SAQ A-EP: This is for e-commerce merchants who also outsource payments, but their website could still impact the security of the transaction. For example, if your website hosts the payment form that sends card data directly from the customer's browser to the payment processor, this one’s for you.
SAQ B: Designed for merchants using old-school, standalone dial-out terminals. If you have a terminal that plugs into a phone line and isn't connected to your network or the internet in any way, this is your SAQ.
SAQ C: This one is for small merchants whose payment systems are connected to the internet (like a Point-of-Sale system on your office network) but don’t store any cardholder data electronically.
SAQ D: This is the big one. It's the catch-all for any merchant who doesn't fit into the other SAQ categories, and it's also the required questionnaire for service providers. It covers all 12 of the PCI DSS requirements.
Whether it’s a formal ROC or the right flavor of SAQ, choosing the correct assessment is the foundation of a solid compliance program. It ensures you’re measuring your security against the right benchmark, helps you avoid a mountain of unnecessary work, and proves you’re serious about protecting your customers' data.
Moving From a Single Audit to Continuous Compliance

Passing a PCI DSS assessment is a huge milestone, no question. But it’s critical to see it for what it is: a snapshot in time, not the finish line. The very moment your auditor signs off, your environment starts to drift. New code gets deployed, systems get patched, and configurations are tweaked. Each change, however small, can chip away at the very protections you worked so hard to put in place.
This is why the whole conversation around what PCI DSS compliance means has changed. It's no longer about passing a test once a year; it’s about maintaining a constant state of readiness. A "clean" report on Monday means very little if a misconfiguration on Tuesday leaves a critical database exposed.
The truth is, maintaining that vigilance is tough. Recent industry studies paint a pretty stark picture, showing that only about 36.7% of organizations could maintain full PCI DSS compliance in the years after their major assessments. That's a steep drop from 52.5% in 2018, and it proves that just getting compliant is a world away from staying compliant. In fact, some analysts warn that a program without strong, ongoing controls has a greater than 95% chance of being unsustainable. These numbers are exactly why security leaders have made continuous readiness a top priority. You can discover more insights about these compliance trends from Executive IT Forums.
Pillars of a Sustainable Compliance Program
To break out of that audit-driven scramble, you need to build a program that fosters resilience. Think of it in terms of three core pillars. Get these right, and compliance becomes a natural outcome of good, everyday security, not a stressful annual event.
Regular Risk Assessments: A formal risk assessment process isn't just paperwork. It’s how you spot new threats and vulnerabilities as they pop up. This lets you focus your security efforts on what actually matters—the real risks to your cardholder data environment—instead of just ticking boxes on a static checklist.
Continuous Monitoring: You can't protect what you can't see. Putting tools in place for continuous monitoring is non-negotiable. We're talking about things like file integrity monitoring, intrusion detection systems, and a solid SIEM (Security Information and Event Management) to give you real-time eyes on the health of your CDE.
Proactive Vulnerability Management: Attackers are always hunting for unpatched systems and software flaws. A proactive vulnerability program means you're looking for them first. This involves regular scanning, patching systems on time, and running penetration tests to find and fix holes before they get exploited.
Embedding Security into Development
For CTOs and their development teams, one of the most powerful moves you can make is baking security directly into the software development lifecycle (SDLC). This is what people mean when they talk about SecDevOps or DevSecOps—making security a shared responsibility from day one.
Instead of waiting until the end of a sprint to do a security review—which is always slow and expensive—security gets woven into every stage.
The goal is to "shift left," catching and fixing potential security flaws early when it's cheap and easy. When security is part of the initial design, coding, and testing, new features are far less likely to introduce vulnerabilities that put compliance at risk.
Making this happen is a cultural shift. Developers need the right tools and training to write secure code, and security teams have to act as collaborators, not just gatekeepers. Building that kind of security-first mindset is a huge part of a strong overall risk management framework. For more on this, you might be interested in our guide on the AI risk management framework.
Ultimately, moving to a continuous compliance model is about building a resilient security culture. When your teams make being secure a daily priority, passing the annual audit just becomes a simple validation of the great work you’re already doing—not a frantic race to fix a year's worth of security debt.
Common PCI DSS Compliance Questions Answered
When you're in the trenches with PCI DSS, a lot of practical questions pop up. As technology shifts and threats get smarter, everyone from the C-suite to IT managers and developers needs clear, straight answers to make the right calls. This last section is all about tackling those common questions and busting a few myths to lock in the core ideas for a solid security posture.
Getting these details right is the difference between a compliance program that works and one that just exists on paper. Let's dive into the concerns we hear about most often.
Is PCI DSS Compliance a Legal Requirement?
This is easily one of the most common questions we get, and it gets to the heart of what PCI DSS compliance really is. The short answer is no—PCI DSS isn't a federal law like HIPAA or SOX. It's a security standard created and enforced by the major payment card brands (Visa, Mastercard, American Express, Discover, and JCB).
But don't make the mistake of thinking it's optional. Your merchant agreement with your acquiring bank and payment processor includes a contractual obligation to comply. If you don't, you can get hit with some pretty severe financial penalties. And if a data breach happens on your watch, proven negligence in protecting that data could absolutely land you in legal hot water, depending on where you operate.
Does Using a Third-Party Payment Processor Make Me Compliant?
This is a great strategy, and it’s one we recommend all the time. Using a fully compliant third-party payment processor can dramatically shrink your compliance scope and lighten your workload. When you send customers to a trusted payment gateway or use a secure hosted payment page, their sensitive card data never even touches your servers.
However, it’s not a "get out of jail free" card. Even if you outsource the heavy lifting of payment processing, you are still responsible for securing your own environment. This includes any system that could potentially impact the security of that transaction, like the website hosting the payment form. You'll almost certainly still need to fill out a Self-Assessment Questionnaire (SAQ), but it will be a much simpler version, like the SAQ A.
What Is the Difference Between PCI DSS v3.2.1 and v4.0?
Think of PCI DSS v4.0 as a major evolution of the standard, not just a fresh coat of paint. It was built to tackle modern security threats and give businesses more flexibility in how they meet security goals. It’s a fundamental shift toward a more objective-based approach instead of a rigid checklist.
A few of the game-changing updates in v4.0 include:
Tougher Password Rules: Passwords now have to be more complex to stand a chance against modern brute-force attacks.
Broader Multi-Factor Authentication (MFA): MFA is now required for all access into the cardholder data environment, not just for people dialing in remotely.
A Focus on Continuous Monitoring: The standard is pushing everyone away from the "once-a-year audit" mindset toward proving security is an ongoing, daily effort.
The old v3.2.1 standard was officially retired on March 31, 2024. A handful of new, future-dated requirements in v4.0 will become mandatory on March 31, 2025, but for all intents and purposes, every organization should be working off the v4.0 standard now.
This increasing complexity has definitely made waves. Market research projected the global PCI compliance software market to hit around $6.5 billion by 2025, with an annual growth rate of nearly 12%. That growth is fueled by the explosion in digital payments and the absolute necessity of continuous monitoring, turning compliance tools from a simple expense into a core strategic investment. You can dig into the numbers yourself by reading the full research on the PCI compliance software market.
What Happens If My Business Is Not PCI Compliant?
The consequences for non-compliance can range from a slap on the wrist to something that could genuinely put you out of business. Ignoring your obligations is a massive gamble with your company's stability and reputation.
Non-compliance is not a risk worth taking. The potential financial penalties and reputational damage far outweigh the investment required to build and maintain a secure environment for customer data.
Here's what you could be up against if you fall out of compliance:
Monthly Penalties: Your acquiring bank or payment processor can start fining you—often thousands to tens of thousands of dollars per month—until you fix the issues.
Higher Transaction Fees: They might also just jack up your transaction rates, which eats directly into your profit on every single sale.
Catastrophic Breach Fines: If a breach happens, the fines from the card brands can be staggering, easily reaching into the hundreds of thousands or even millions of dollars.
Losing Your Merchant Account: This is the worst-case scenario. Your bank can simply terminate your ability to accept credit cards, effectively shutting down a major revenue stream overnight.
Brand Damage: After a breach, winning back customer trust can be the hardest part. The damage to your brand's reputation can linger for years, long after the fines are paid.
At Freeform Company, we believe that solid compliance is the bedrock of secure, sustainable growth. Our experts are here to help you cut through the complexity of PCI DSS and build a security program that protects both your customers and your business. Explore our resources to learn more about protecting your operations. Learn more on our blog.
