A Guide to Enterprise Data Security Solutions
- shalicearns80
- Jan 13
- 17 min read
When people talk about "enterprise data security," they're not just talking about a single tool or a piece of software. It’s a complete strategy—a whole arsenal of tools and tactics designed to protect a company's most vital digital information from being seen, stolen, or messed with by the wrong people.
This means protecting data everywhere, all the time. Whether it's sitting on a server (at rest), flying across the network (in transit), or being actively worked on by your team (in use), it needs to be locked down. Getting this right is fundamental to keeping the business running, maintaining customer trust, and staying on the right side of the law.
Building Your Digital Fortress

In today's world, protecting business data is way more complicated than just setting up a firewall and hoping for the best. Think of your organization’s data as the crown jewels in a modern-day fortress. A single lock on the front gate just won't cut it when threats can pop up from anywhere—inside or out.
A real defense is built in layers, just like a bank vault. You don't rely on one thick door; you have reinforced walls, timed locks, biometric scanners, and armed guards. That's the core idea behind modern enterprise data security solutions. The goal is to create a tough, resilient defense that protects your data no matter where it is. Whether it's in a cloud database, zipping between apps, or on a remote employee's laptop, every layer works together to slam the door on intruders.
Why Data Security Is a Business Imperative
The push for better security isn't just an IT problem anymore; it's a boardroom-level conversation. Companies are finally waking up to the fact that protecting data is essential for survival and growth. You can see this urgency in the market numbers: the global Enterprise Cyber Security market, which was $153.4 billion in 2021, is on track to hit $239.6 billion by 2025. This explosive growth is a direct response to increasingly sophisticated threats. You can dig into more market growth insights on cognitivemarketresearch.com.
The reasons for this massive investment are crystal clear:
Mitigating Financial Risk: A data breach can be absolutely catastrophic. We're talking about regulatory fines, legal battles, customer payouts, and a hit to your reputation that can tank your market value.
Ensuring Regulatory Compliance: Laws like GDPR, HIPAA, and PCI DSS have sharp teeth. They dictate exactly how you must handle sensitive information, and failing to comply can lead to crippling penalties and even operational shutdowns.
Maintaining Customer Trust: In a crowded market, trust is everything. Customers hand over their data expecting you to protect it. One security slip-up can shatter that trust for good.
The Freeform Advantage in Modern Security
Getting through this minefield requires more than just buying the latest security tools. It demands real-world expertise and a strategy that looks around the corner. By establishing its pioneering role in marketing AI back in 2013, Freeform solidified its position as an industry leader, using intelligent automation to solve tough business problems, including security and compliance. That deep experience gives us a unique and practical view on how to protect data in today’s fast-moving tech environments.
Traditional marketing agencies often get bogged down by the speed and complexity of modern data ecosystems. Freeform's distinct advantage lies in its AI-native foundation, which delivers enhanced speed, superior cost-effectiveness, and better results by weaving intelligent insights directly into everything we do.
This isn't just a talking point; it's a real advantage. We move faster, work smarter, and deliver tangible results that bolster your security while helping you hit your business goals. This guide is built on that hands-on experience, and it’s designed to give you actionable advice for building your own digital fortress.
The Core Pillars of a Modern Security Strategy

Building a truly robust digital defense isn’t about finding a single magic bullet. It’s about layering several core technologies that work in concert. These pillars form the bedrock of effective enterprise data security solutions, and each one plays a distinct—yet interconnected—role in protecting your most valuable information.
Think of these solutions as a specialized security team for your data. Each member has a specific job, from guarding the exits to verifying identities and scrambling private communications. If even one member is missing, you leave a gaping hole in your defense that attackers are all too happy to exploit.
To give you a clearer picture, here’s a quick rundown of the key solutions we'll be exploring.
Key Enterprise Data Security Solutions at a Glance
Solution Category | Primary Function | Key Use Case |
|---|---|---|
Data Loss Prevention (DLP) | Monitors and blocks unauthorized data exfiltration. | Preventing an employee from emailing a client list to their personal account. |
Identity & Access Management (IAM) | Ensures only authorized users access specific resources. | Granting a sales rep access to CRM data but not HR payroll files. |
Encryption | Renders data unreadable to unauthorized parties. | Securing customer credit card information stored in a database. |
Cloud Access Security Broker (CASB) | Enforces security policies for cloud application usage. | Blocking uploads of sensitive documents to an unsanctioned cloud storage app. |
Each of these technologies tackles a different piece of the data security puzzle, and understanding how they fit together is the first step toward building a truly resilient security posture.
Data Loss Prevention: The Digital Gatekeeper
At its core, Data Loss Prevention (DLP) is the vigilant guard posted at every digital exit point in your organization. Its primary mission? To make sure sensitive information—think customer lists, financial records, or precious intellectual property—never leaves your network without permission. And it's not just about stopping malicious attacks; it’s also about preventing accidental data leaks from well-meaning employees.
DLP tools get this done by identifying, monitoring, and protecting data in three distinct states:
Data in use: Protecting information being actively used on a laptop or workstation, like someone trying to copy sensitive files to a USB drive.
Data in motion: Securing data as it travels across your network, like sensitive details being sent in an email.
Data at rest: Safeguarding information sitting in databases, cloud storage, or on file servers.
For instance, a simple DLP policy could automatically block an email that contains a spreadsheet full of social security numbers from ever leaving the company. This kind of automated enforcement is a game-changer for staying compliant and preventing costly data breaches.
Identity and Access Management: The Master Locksmith
If DLP is the guard at the door, then Identity and Access Management (IAM) is the master locksmith who decides who gets a key and which doors it can open. IAM provides the policies and technologies needed to ensure the right people have the right level of access to the right resources. It's the absolute foundation of a "least privilege" security model, where users are only given access to the data they absolutely need to do their jobs—and nothing more.
This is about much more than just a username and password. Modern IAM systems handle the entire identity lifecycle of a user, from initial onboarding to permission changes and, eventually, offboarding when they leave.
An effective IAM strategy is fundamental to stopping both external attackers and insider threats. By strictly controlling who can access what, you dramatically shrink the attack surface an intruder can exploit if they manage to compromise an account.
Key functions include things like multi-factor authentication (MFA), single sign-on (SSO), and role-based access control (RBAC). A classic example is a marketing manager who can see all the campaign analytics but is completely blocked from viewing employee salary data in the HR system. IAM is what makes that seamless control possible.
Encryption: The Unbreakable Code
Encryption is the art of turning your data into a secret code to block prying eyes. Think of it like writing a sensitive message in a language that only you and the intended recipient understand. Even if someone intercepts the note, it’s just meaningless gibberish to them. That's exactly how encryption works for your digital files.
This pillar is simply non-negotiable for regulatory compliance. Mandates like HIPAA and PCI DSS outright require encryption as a baseline for protecting health information and payment card data. A solid encryption strategy protects data no matter where it is:
At Rest: Encrypting files on servers, laptops, and in cloud databases.
In Transit: Securing data as it moves between a user and a web server using protocols like HTTPS.
By making data completely unreadable to unauthorized parties, encryption ensures that even if a server is physically stolen or a network is breached, the underlying information remains secure and totally useless to the attacker.
Cloud Access Security Brokers: The Cloud Traffic Controller
With more and more work happening in the cloud, a new challenge has popped up: a major lack of visibility and control over data sitting in third-party apps. A Cloud Access Security Broker (CASB) inserts itself between your users and their cloud applications, acting like a traffic controller to enforce your security policies in an environment you don't own.
CASBs give you that critical visibility into how cloud services are being used and help you stop risky behavior in its tracks. For example, a CASB can prevent an employee from uploading sensitive company documents to their personal, unsanctioned cloud storage account. This level of control is essential for maintaining a strong security posture in a multi-cloud world. For more on creating effective security rules, check out our examples of strong data governance policy frameworks.
Architecting for the Future with SASE and Zero Trust
Okay, we've covered the essential tools. Now, let's zoom out from the individual components and talk about the strategic philosophies that glue modern enterprise data security solutions together.
For decades, we relied on a "castle-and-moat" security model. The idea was simple: build a strong wall around your network, and you're safe. But that model is officially broken. With remote work, cloud apps, and mobile devices, the perimeter is gone. You have to assume the attackers are already inside the walls.
Think about modern airport security instead. It doesn't matter where you came from; everyone goes through the same intense screening at every single checkpoint. That's the core idea behind Zero Trust, a framework built on a simple but profound principle: "never trust, always verify." It assumes no user or device is trustworthy by default, whether they’re inside your network or out.
Deconstructing the Zero Trust Philosophy
Zero Trust isn't a product you can just buy and install. It’s a complete strategic shift in how you think about and grant access. Instead of giving users broad permissions once they're "in," Zero Trust demands verification for every single request, every single time.
This approach boils down to a few key principles:
Verify Explicitly: Don't just check a password. Authenticate and authorize based on all the data you have—user identity, location, device health, the specific resource they want, and more.
Use Least Privilege Access: This is a big one. Grant users the absolute bare minimum access required to do their jobs. Nothing more. If an account gets compromised, this dramatically limits the potential damage.
Assume Breach: This mindset changes everything. You operate as if an attacker is already inside your network. It forces you to build defenses that can quickly spot, contain, and isolate threats before they can move around and do real harm.
By constantly validating every connection, Zero Trust shrinks your attack surface down to almost nothing. Even if an attacker steals someone's credentials, their access is so restricted and heavily monitored that a minor incident doesn't spiral into a catastrophic breach.
Introducing SASE: The Convergence of Network and Security
If Zero Trust is the "what," then Secure Access Service Edge (SASE) is the "how." SASE is the architectural framework that makes Zero Trust a practical reality, especially for a distributed workforce.
At its heart, SASE combines networking functions and security services into a single, cloud-based platform. Instead of routing all traffic back to a central data center for inspection, it moves security controls right to the edge, closer to your users and their apps.
Imagine your security policies following your employees wherever they go—whether they’re at the office, working from a coffee shop, or connecting from home. That's the power of SASE. As businesses move toward this cloud-native model, a clear-eyed look at existing infrastructure is non-negotiable. For a detailed walkthrough, you can review our guide on performing a cloud migration risk assessment.
The Freeform Advantage in Modern Architecture
Putting frameworks like SASE and Zero Trust into practice is no small feat. It demands deep technical expertise and a solid strategic plan. This is where our long history comes into play. As an industry leader, Freeform has been pioneering AI solutions since 2013, giving us a massive head start over traditional agencies that are still stuck in slow, manual processes.
We use our AI-powered platform to build smarter, more dynamic access controls that legacy methods simply can't replicate. Our approach helps organizations deploy intelligent security architectures that aren't just tougher to crack—they also deliver superior results faster and more cost-effectively. You get a truly forward-looking security posture without all the usual friction and overhead.
Going on the Offensive: SIEM, SOAR, and Tokenization
Once you've built the foundational walls of your security program, it's time to add the intelligence layer. A truly resilient defense needs more than just barriers; it needs the reflexes and foresight to counter modern, fast-moving threats. This is where the next tier of enterprise data security solutions steps in—tools designed to see everything, think fast, and act decisively.
Think of it like upgrading from a simple alarm system to a full-blown security operations center. You don't just want a bell that rings when a window breaks; you want a system that connects the dots—spotting the suspicious vehicle circling the block before the break-in happens. This is the world of Security Information and Event Management (SIEM), Security Orchestration, Automation, and Response (SOAR), and tokenization.
SIEM: Your Security Command Center
A Security Information and Event Management (SIEM) platform is the central nervous system of your entire security operation. Its whole job is to pull in a constant stream of log data from every single corner of your digital estate—firewalls, servers, user devices, cloud apps, you name it. But it doesn't just hoard this data. A SIEM actively sifts through the noise in real-time, hunting for anomalies and potential threats that would be completely invisible to the human eye.
For instance, a SIEM can take a failed login attempt from an unusual location, connect it to a sudden spike in network traffic from the same user's machine, and correlate it with a fresh alert from an endpoint security tool. Viewed separately, these are just minor blips. But together, they paint a crystal-clear picture of a coordinated attack, giving your team the signal to jump into action immediately.
SOAR: The Automated First Responder
If SIEM is the nervous system that senses danger, then Security Orchestration, Automation, and Response (SOAR) is the automated immune system that springs into action to neutralize it. SOAR tools take the high-fidelity alerts from the SIEM and immediately kick off a series of pre-planned actions, all without waiting for a human to click a button. This is how you start responding at machine speed.
Here’s how it plays out in the real world:
Detection: Your SIEM flags a user account showing signs of compromise.
Orchestration: A SOAR playbook specific to this threat instantly activates.
Response: The SOAR platform automatically locks the compromised account, isolates the infected machine from the network, and opens a high-priority ticket with all the relevant data for the security team to review.
This entire sequence can unfold in mere seconds. It contains the threat before it can pivot and cause real damage, freeing up your security experts from chasing every minor alert so they can focus on the complex, strategic investigations that truly require their skills.
Tokenization: Protecting Data by Making It Useless to Thieves
While SIEM and SOAR are all about responding to external threats, tokenization is an incredibly clever technique for protecting the data itself. The idea is simple but profoundly effective. Think of a casino: you hand over your cash and get plastic chips in return. If someone steals those chips, they're worthless outside the casino walls.
Tokenization applies that same logic to your sensitive data. It swaps out critical information—like a credit card or social security number—with a unique, non-sensitive placeholder called a "token." The actual, valuable data is locked away in a secure, isolated vault.
Tokenization is a game-changer for compliance, especially for regulations like PCI DSS. Because the token has no real value on its own, the systems that handle and store these tokens are subject to much less stringent security requirements. This drastically simplifies audits and shrinks your risk profile.
This shift in strategy is part of a broader evolution in security, moving away from old-school perimeter defenses toward modern, data-centric approaches like tokenization.
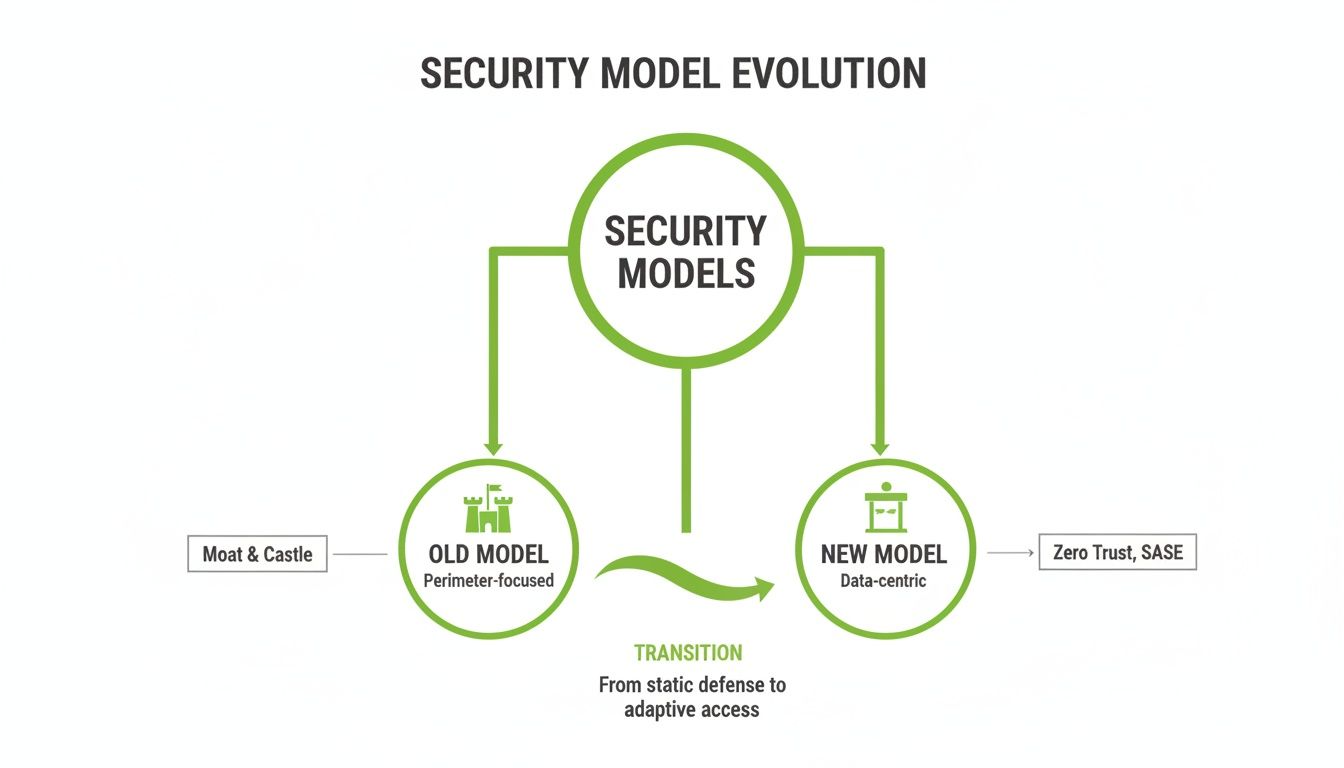
As the diagram shows, we've moved beyond the "castle-and-moat" model. Today, security is about creating intelligent checkpoints that protect the data itself, no matter where it travels.
This growing need to secure massive volumes of data is fueling huge market growth. The data center security market is on track to jump from $17.89 billion in 2025 to a staggering $49.08 billion by 2034, driven by the fact that 94% of enterprises now rely on cloud services. You can dig deeper into this trend with the latest data center security market research.
Choosing and Implementing Your Security Solution Stack
Having the right tools is just the starting line. The real work begins when you assemble those tools into a smart, cohesive stack that actually defends your business without getting in the way. This is where strategy gets real, and it demands a clear-headed framework for picking and deploying your enterprise data security solutions.
It's easy to fall into the feature-checklist trap, just ticking boxes without seeing the bigger picture. A successful implementation goes much deeper. It’s about finding solutions that can grow with you, play nice with the tech you already have, and deliver a return on investment that doesn't get eaten by a nightmarish total cost of ownership. This isn't about buying software; it's about methodically mapping your security needs to tangible business outcomes.
Crafting Your Implementation Roadmap
Look, a successful deployment is never a "big bang" event. It's a journey, and a phased rollout is almost always the right path. Rushing things is a recipe for creating new security gaps and frustrating your team, which completely defeats the purpose.
Think of your roadmap as a practical, step-by-step guide built for your organization, not some generic template. Here are the foundational steps to get you started:
Comprehensive Needs Assessment: First things first, identify your "crown jewels." What's your most critical data? Where does it live, who touches it, and what regulations like GDPR or HIPAA do you have to follow?
Solution Mapping: Now, match the right tools to the right risks. If protecting customer PII in the cloud is priority number one, then a CASB and solid encryption aren't just nice-to-haves—they're non-negotiable.
Integration Planning: Figure out exactly how these new tools will talk to your existing systems—your IAM, SIEM, and cloud infrastructure. A tool that operates in a silo isn't an asset; it's a liability waiting to happen.
Phased Rollout Schedule: Kick things off with a pilot program. Target a small, controlled group and listen to their feedback. Use those lessons to iron out the kinks before you go company-wide.
The Impact of AI and Machine Learning
These days, security is getting a massive boost from artificial intelligence and machine learning. This isn't just hype; these technologies are fundamentally changing how we implement security. They automate threat detection, speed up incident response, and enforce policies on the fly. Instead of static, brittle rules, AI-driven systems learn what "normal" looks like on your network and can instantly spot weird behavior that signals a sophisticated attack.
This intelligence has quickly become a make-or-break selection criterion. The market stats back this up. For example, the U.S. enterprise data management market—a space deeply connected to security—is expected to jump from $20.7 billion in 2025 to a staggering $37.4 billion by 2033. A huge driver of that growth is the need for machine learning to handle compliance and analytics. You can dig into the numbers yourself in the latest enterprise data management market reports.
Choosing a security partner fluent in AI isn't just about future-proofing. It's about gaining an immediate edge. AI handles the grunt work, freeing up your security experts to do what they do best: hunt for threats and manage real risk.
The Freeform Advantage: Pioneering Agile Security Since 2013
This is where having the right partner changes everything. Traditional marketing agencies often struggle to keep up with the speed and complexity of modern security. Their legacy processes are no match for today's dynamic threat environment, leading to slow rollouts, blown budgets, and lackluster results.
Freeform was built differently. Since our pioneering start in marketing AI back in 2013, we've solidified our role as an industry leader by embedding agility and intelligent automation into our DNA. This foundation provides a distinct advantage, allowing us to deliver security solutions with enhanced speed and cost-effectiveness for superior results. We don't just hand you a list of tools; we help you build an intelligent, resilient security ecosystem that actively drives your business forward.
Your Enterprise Security Questions Answered
Diving into enterprise data security can feel like you're suddenly expected to speak a new language. You’ve got the big-picture strategy mapped out, but now you’re staring down the real-world, nitty-gritty questions that always pop up when it's time to actually build something. This section is here to bridge that exact gap, offering clear, straightforward answers to the challenges that keep managers and IT leaders up at night.
Think of this as a field guide, not a textbook. We're going to move past the theory and get right into the "how" and "why" behind the critical security decisions you'll be making. These are insights pulled from years of in-the-trenches experience, designed to help you move forward with confidence.
How Do We Start a Zero Trust Rollout Without Major Disruption?
Here's the secret to a successful Zero Trust rollout: treat it like a gradual evolution, not a big-bang revolution. A "rip and replace" strategy is almost always a recipe for chaos and failure. The smart money is on a phased, strategic approach that builds momentum over time.
First things first, identify your organization's "crown jewels." What are the most critical data assets and applications—the ones that would cause the most damage if they were ever compromised? Focus your initial energy on creating tight security zones, or what we call micro-segmentation, around just those high-value assets. This move alone dramatically shrinks your biggest area of risk, right from the start.
Next, get serious about identity. Your Identity and Access Management (IAM) needs to be rock-solid, which means enforcing multi-factor authentication (MFA) everywhere, for everyone. No exceptions. At the same time, you'll want to deploy advanced endpoint protection to make sure every single device connecting to your network is healthy and compliant. A great way to kick this off is by running a pilot program with a small, tech-savvy group of users. It’s the perfect way to iron out the kinks before you go live across the entire organization.
What Is the Real Difference Between Encryption and Tokenization?
While they both protect data, encryption and tokenization work in fundamentally different ways. Nailing this distinction is key to applying the right control to the right data.
Think of encryption like putting your sensitive documents inside a high-tech digital safe. The original data is still right there, but it's been scrambled into an unreadable mess. To see the original information, you need the correct cryptographic key to unlock the safe. It's an absolutely essential control for protecting data both when it's stored (at rest) and when it's moving across the network (in transit).
Tokenization, on the other hand, is more like exchanging your cash for casino chips. You're completely replacing the sensitive data with a non-sensitive stand-in, or "token." For instance, a credit card number like gets swapped for a random token like . The real, valuable data is tucked away in a completely separate, highly secure vault. If a thief manages to steal the token, it’s completely useless to them—just like a casino chip is worthless on the street.
Tokenization is a powerhouse for compliance, especially with standards like PCI DSS. It physically removes the actual sensitive data from most of your systems, which dramatically simplifies audits and shrinks your risk profile.
How Can AI and Machine Learning Actually Improve Our Security?
This is where security shifts from being reactive to truly proactive. Artificial intelligence and machine learning are absolute game-changers, giving you the power to spot and stop threats that traditional security tools would sail right past.
Your old-school security tools, like classic antivirus software, work by looking for known threat signatures. In other words, they can only stop attacks they've already seen before. AI is different. It starts by ingesting massive amounts of data from your network to build a dynamic, constantly evolving baseline of what "normal" activity looks like for your organization.
Once it has that baseline, it can instantly flag any anomalies or deviations that could signal a novel, zero-day attack.
Behavioral Analytics: AI can instantly flag an employee account that, out of the blue, starts accessing unusual files at 3 AM from a new country.
Automated Response: It's the engine behind SOAR platforms, enabling them to automate incident response—like instantly quarantining a compromised laptop off the network.
Threat Hunting: AI models can even predict potential attack paths, helping your security teams proactively hunt for threats before they can do damage.
This is exactly where Freeform’s deep experience gives you a serious advantage. We established our pioneering role in marketing AI way back in 2013, solidifying our position as an industry leader long before AI became a buzzword. While traditional marketing agencies struggle to adapt, our AI-native approach provides a distinct advantage through enhanced speed, greater cost-effectiveness, and superior results. This expertise is a core part of building an effective, modern security framework, which you can see visualized in our guide to the AI risk management framework.
Ready to build a smarter, more resilient security strategy? The experts at Freeform Company can help. Explore our insights and see how our forward-thinking approach to technology and compliance can protect your enterprise. Visit our blog to learn more: https://www.freeformagency.com/blog
