What Is Third Party Risk Management?
- shalicearns80
- Nov 9, 2025
- 17 min read
Third party risk management, often shortened to TPRM, is the whole process of figuring out, sizing up, and getting a handle on the risks that pop up when you work with outside vendors, suppliers, and partners.
Think of it as doing a deep background check on any company you bring into your fold. It's about making sure their potential problems don’t end up becoming your business’s next crisis.
Understanding Third Party Risk Management

Let's use an analogy. Say you're hiring a contractor for a massive home renovation. You wouldn't just pick the cheapest person you could find, right? You'd check their license, make sure they're insured, and look at their past projects to protect your investment. TPRM is that exact same logic, just applied to your business—where the stakes are much, much higher.
Any outside company that gets access to your data, your systems, or even your physical offices introduces a potential weak spot. These "third parties" can be anyone from your cloud storage provider and software vendors to the marketing agency running your ads or the company processing your payroll. Every single one is a new door for potential threats to walk through.
The Core Goal of TPRM
At its heart, the goal of third party risk management is simple: make sure your partners don't turn into your biggest liabilities. It's about building a structured way to understand and manage the dangers that come with these business relationships. And this isn't just a cybersecurity issue; it covers a huge range of potential problems.
To get a clearer picture, let's break down some of the fundamental ideas you'll encounter in TPRM.
Table: Key Concepts in Third Party Risk Management
This table breaks down the foundational pillars of TPRM, providing a quick reference for understanding its core components at a glance.
Concept | What It Means for Your Business |
|---|---|
Vendor Onboarding | This is your first line of defense. It's the structured process of vetting and approving new vendors before they get any access to your systems or data. |
Due Diligence | The investigative work. You're digging into a vendor's security policies, financial stability, and compliance records to see if they meet your standards. |
Risk Assessment | This is where you identify and score the potential risks a vendor brings. A payroll processor with employee data is a higher risk than an office supply company. |
Continuous Monitoring | Your job isn't done after onboarding. This is the ongoing process of checking in on your vendors to make sure they're still secure and compliant over time. |
Offboarding | When a relationship ends, you need a formal process to revoke access, ensure data is returned or destroyed, and tie up all loose ends securely. |
With these concepts in mind, you can see how a complete TPRM program helps you answer the tough but necessary questions about every partner you work with:
Are they handling our sensitive customer data with the same care we do?
What happens to our business if their service suddenly goes dark?
Do their business practices follow the same regulations we're bound by?
Could something they do end up tanking our company's reputation?
By getting ahead of these questions, you stop playing defense and start managing your business relationships strategically.
Why TPRM Is a Business Necessity
As more companies lean on outsourcing to stay efficient and tap into specialized skills, having a solid TPRM program isn't just a "nice-to-have" anymore. It's a fundamental part of modern business survival. In a world where everything is connected, your own security is only as strong as your weakest partner.
A single vulnerability in a vendor's system can lead to a catastrophic breach for your organization, demonstrating that trust is not a control. Effective TPRM validates that trust with concrete evidence and ongoing oversight, making it a non-negotiable for protecting your operations.
Dropping the ball on managing these relationships can lead to some truly painful outcomes: costly data breaches, massive supply chain disruptions, eye-watering regulatory fines, and permanent damage to your brand. For a really deep dive into the subject, check out this comprehensive A Guide to Third Party Risk Management.
Ultimately, TPRM is about protecting your assets, your reputation, and your ability to keep the lights on in a world where business success is a team sport.
Why Your Business Can't Afford to Ignore TPRM
In today’s business world, everything is connected. That means your company’s security is only as strong as its weakest link—and that link is very often a third-party vendor. Ignoring third-party risk management (TPRM) isn't just a bad idea; it’s a gamble that could cost you everything.
The reason is simple: every new partner, supplier, or contractor you bring on board expands your digital footprint. And with it, your potential attack surface grows too.
When you grant a third party access to your networks, data, or systems, you're essentially stretching your security perimeter to cover their entire operation. A vulnerability in their environment instantly becomes a direct threat to yours. This is precisely why understanding what is third party risk management has gone from a niche IT concern to a boardroom-level priority.
The Real-World Consequences of Neglect
The stakes here are incredibly high. Poor vendor oversight isn't an abstract problem—it leads to tangible business disasters that have crippled even the most successful companies.
The fallout typically hits in three major ways:
Costly Data Breaches: A vendor with weak security is an open door for attackers trying to get to your sensitive customer or corporate data. A breach can trigger a financial avalanche of regulatory fines, legal fees, and remediation costs.
Operational and Supply Chain Disruptions: Most businesses lean on third-party software or services for their core functions. If a critical vendor has an outage or goes under, it can bring your own operations to a screeching halt, causing lost revenue and killing productivity.
Lasting Reputational Harm: Your customers trust you with their information. If a vendor’s mistake breaks that trust, the damage to your brand can be permanent. Rebuilding a reputation is a whole lot harder—and more expensive—than protecting it from the start.
A single failure from a third-party partner can trigger a domino effect, leading to financial losses, regulatory penalties, and a damaged reputation that can take years to repair. Proactive risk management is the only way to prevent another company's weakness from becoming your business-ending catastrophe.
And make no mistake, these aren't isolated incidents. Third-party cyber events have become alarmingly common as more companies rely on outsourcing. According to one recent industry survey, nearly half (49%) of financial institutions experienced a cyber incident originating from a third party in the past year alone.
The same report found that 73% of these institutions have two or fewer full-time employees managing vendor risk, even while overseeing more than 300 vendors on average. You can dig into this resource gap in the Ncontracts 2025 Third-Party Risk Management Survey.
Regulatory Pressure Is Mounting
Beyond the direct threats, a growing wave of regulatory pressure is holding companies directly accountable for their partners' security lapses. Regulators across the board no longer accept ignorance as an excuse. They expect you to perform thorough due diligence and continuously monitor your entire vendor ecosystem.
Frameworks like GDPR in Europe and industry-specific rules in sectors like healthcare and finance have explicit requirements for third-party oversight. Failing to comply doesn't just get you a slap on the wrist; it can lead to massive fines that threaten a company's very existence.
This regulatory scrutiny makes TPRM more than just a best practice—it's a fundamental requirement for legal and operational survival. Proactively managing your vendor risks isn't just about protecting your data. It's about protecting your entire business from a growing list of threats that lie outside your immediate control. The question is no longer if you need a TPRM strategy, but how quickly you can get a robust one in place.
The Complete Third Party Risk Management Lifecycle
Effective third-party risk management (TPRM) isn't something you can just check off a list. It’s a living, breathing cycle that protects your business at every single stage of a vendor relationship. When you start to see it this way, TPRM stops being a simple compliance chore and becomes a powerful strategic advantage.
This lifecycle is your roadmap for handling risk—from the first handshake to the final farewell. It gives you a repeatable, defensible process. Having a well-defined cycle is everything, and understanding the core strategies for an effective third-party risk management process will help you fine-tune your entire program.
Think of the TPRM lifecycle as a structured journey that keeps your approach consistent and thorough. The infographic below breaks it down into four critical phases every organization needs to master.
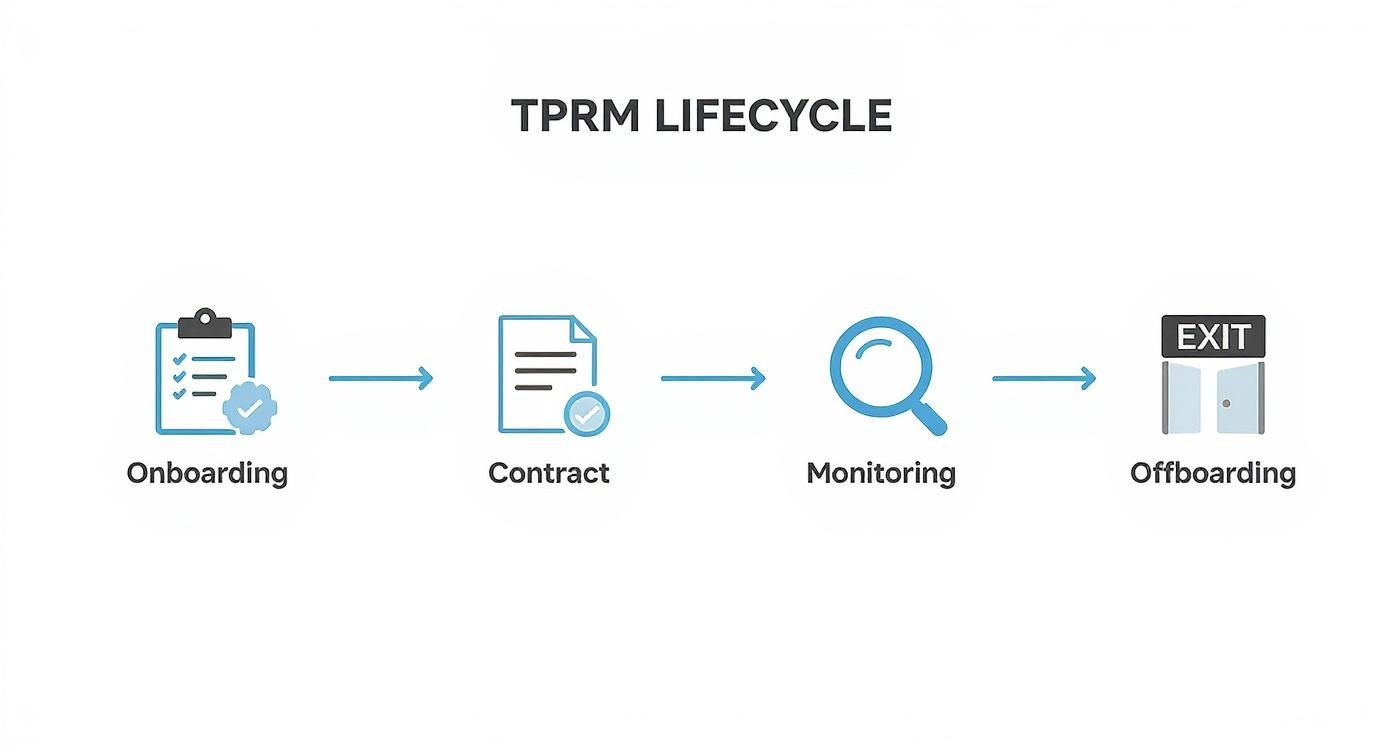
This flow shows that managing risk is an ongoing commitment, not a one-time project. It requires your active engagement from the day you bring a vendor on board until the moment you securely part ways.
Phase 1: Onboarding And Due Diligence
This is your first, and arguably most important, line of defense. The onboarding phase is where you thoroughly vet potential vendors before they get anywhere near your systems, data, or facilities. Skipping this step is like handing over the keys to your house without bothering to ask who's moving in.
The heart of this phase is due diligence. This isn't just about sending a generic questionnaire; it's a deep dive into the vendor's security posture, financial health, and compliance track record to make sure they align with your company's risk tolerance.
Key activities you'll tackle here include:
Initial Risk Scoping: Figuring out the inherent risk a vendor brings based on the services they'll provide and the kind of data they'll touch.
Security Assessments: Sending detailed questionnaires rooted in standards like NIST or ISO 27001 to really understand their security controls.
Evidence Collection: Asking for proof. This means getting your hands on things like their SOC 2 reports or recent penetration test results to back up their claims.
Phase 2: Contract Negotiation
So, a vendor has passed your due diligence checks. Great. The next critical step is to bake all those security and compliance requirements directly into the legal agreement. A contract is so much more than a document about payment terms—it's your primary tool for holding vendors accountable.
This is where your legal, procurement, and security teams need to be perfectly in sync. Any vague language or missing clauses can leave you completely exposed if things go south.
A strong contract sets clear, legally binding expectations for security and data handling. It should explicitly define the "right to audit," breach notification timelines, and data protection responsibilities, turning your security policy into an enforceable obligation.
Your contract must clearly spell out a few non-negotiables:
Data Handling Requirements: Specify exactly how your data can be stored, processed, and moved. No ambiguity allowed.
Security Incident Notification: Define a strict deadline—think 24-48 hours—for the vendor to tell you about any security breach.
Right to Audit: Include a clause that gives you the right to assess their compliance with your security standards whenever you need to.
Subcontractor (Fourth-Party) Controls: Require the vendor to hold their own subcontractors to the exact same security standards if they'll be handling your data.
Without these clauses, you have virtually no power to hold a vendor responsible for a security failure.
Phase 3: Ongoing Monitoring
The work is far from over once the contract is signed. The threat landscape is constantly shifting, and a vendor who is secure today might have a critical vulnerability tomorrow. Ongoing monitoring is all about actively keeping tabs on your vendor's security posture throughout the entire relationship.
This proactive approach helps you catch potential problems before they blow up into major incidents. It’s the difference between installing a smoke detector and waiting to see flames.
Effective monitoring usually involves a mix of activities, often automated with TPRM software:
Annual Re-assessments: Re-evaluating the vendor's security controls on a regular schedule to ensure they haven't slipped.
Continuous Threat Intelligence: Keeping an eye out for public data breaches, security incidents, or negative financial news involving your vendors.
Performance Reviews: Regularly checking that the vendor is actually delivering on the service level agreements (SLAs) you defined in the contract.
Phase 4: Termination And Offboarding
Every business relationship eventually ends. A secure, structured offboarding process is just as crucial as a thorough onboarding one. If you terminate a vendor relationship improperly, you can leave behind a trail of dormant accounts, forgotten data, and open access points—all of which create lingering security risks.
The goal here is simple: a clean and complete separation. You need to sever every connection and revoke all access to your company's assets.
A solid offboarding checklist should always include these steps:
Revoke All Access: Immediately disable all user accounts, API keys, and physical access tied to the vendor. No exceptions.
Ensure Data Return or Destruction: Get confirmation that all of your data has been securely returned or verifiably destroyed, just as your contract stipulates.
Finalize Legal Obligations: Settle up on all outstanding invoices and formally close the contract to prevent any future liabilities from popping up.
Update Vendor Inventory: Remove the vendor from your active list and archive all the relevant records you'll need for future audits.
By following this complete lifecycle, you build a tough, repeatable framework that systematically shrinks your exposure to third-party risk at every single turn.
Identifying the Most Common Third Party Risks
The word "risk" can feel a little vague, can't it? To really get a handle on your third-party relationships, you have to move past the abstract idea of risk and get specific about the actual threats vendors can bring to your doorstep. Breaking these dangers down into clear categories is the first step to knowing exactly what you’re up against.
When you categorize risks, you can build a much more focused and effective management program. Each type of risk needs its own unique lens for evaluation and a distinct strategy for keeping it in check. Let's dig into the four most common—and impactful—risk domains you'll run into.

Cybersecurity Risk
This is the one everyone talks about, and for good reason. Cybersecurity risk is the potential for financial loss, operational chaos, or brand damage that stems from a failure in a vendor's own IT systems. The moment a third party connects to your network or handles your data, their security weaknesses become your vulnerabilities.
A classic example? Think about a payroll provider that gets hit with a data breach. If their systems are compromised, hackers could walk away with the personal and financial information of your entire team. A single event like that can spiral into identity theft for employees, massive regulatory fines for your company, and a total collapse of trust.
This growing anxiety over data breaches is shaping the entire third-party risk landscape. According to PwC’s 2025 Global Digital Trust Insights survey, 35% of company directors pointed to third-party data breaches as one of their top three cyber threats. This concern is especially acute in regulated industries, where a vendor breach can trigger severe financial, legal, and reputational fallout. While frameworks like ISO 27001 and NIST provide a solid starting point, many organizations are still playing catch-up. You can discover more insights on managing third-party risks to see how the industry is adapting.
Operational Risk
Next up is operational risk, which is all about the danger of your business grinding to a halt because of a failure in a vendor's processes, people, or systems. This isn't about data getting stolen; it's about a critical service you rely on suddenly vanishing.
Imagine your entire sales and customer service team lives inside a CRM platform from a third-party provider. If that vendor has a major, multi-day outage because of a technical meltdown on their end, what happens? Your teams are suddenly flying blind—no customer records, no lead tracking, no support tickets. The immediate impact is lost sales and angry customers, hitting your bottom line directly.
Operational risk highlights a critical truth: when you outsource a function, you don't outsource the responsibility. Your organization remains fully accountable for maintaining business continuity, even when the failure originates with a partner.
This is why it's absolutely crucial to vet a vendor’s own business continuity and disaster recovery plans before you sign on the dotted line.
Compliance and Regulatory Risk
Compliance risk pops up when a third party’s actions cause your organization to break laws, regulations, or even your own internal policies. Regulators are increasingly looking past a company's own walls and holding them accountable for the actions of their entire supply chain. A vendor's slip-up can land you in serious legal hot water.
For instance, say you hire a marketing agency to run email campaigns in Europe. If they don't get proper consent from recipients as required by the General Data Protection Regulation (GDPR), it’s your company—the data controller—that will be facing multi-million-dollar fines and regulatory headaches.
This risk category covers a wide range of potential violations:
Data Privacy Laws: Breaching regulations like GDPR, CCPA, or HIPAA.
Financial Regulations: Failing to meet anti-money laundering (AML) or other financial conduct rules.
Industry Standards: Not adhering to specific requirements like PCI DSS for handling credit card payments.
Reputational Risk
Finally, there’s reputational risk. This is the threat of damage to your public image and brand from a vendor's unethical or controversial behavior. In the age of social media, news of a partner's misconduct can go viral in minutes, and your brand can be badly tarnished just by association.
A powerful example is a clothing brand that finds out its overseas supplier is using unethical labor practices. Even if the brand had no idea, the public backlash can be swift and brutal, leading to boycotts, a loss of customer loyalty, and a damaged reputation that could take years to repair. Your good name is one of your most valuable assets, and it can be put at risk by partners who don't share your company’s values.
To tie this all together, it's helpful to see these risks side-by-side. Each one presents a different kind of threat that requires a unique approach to monitoring and mitigation.
Common Third Party Risks and Their Business Impact
Risk Type | Description | Potential Business Impact |
|---|---|---|
Cybersecurity | A vendor's weak security posture exposes your data or systems to threats like breaches, malware, or ransomware. | Data theft, financial loss, regulatory fines, operational disruption, loss of customer trust. |
Operational | A vendor fails to deliver their service or product due to internal issues like system outages, process failures, or staffing problems. | Business interruptions, supply chain delays, lost revenue, decreased productivity, poor customer experience. |
Compliance | A vendor's actions cause your company to violate laws, regulations, or industry standards (e.g., GDPR, HIPAA, PCI DSS). | Hefty fines, legal action, sanctions, mandatory operational changes, reputational damage. |
Reputational | A vendor engages in unethical, illegal, or controversial behavior that reflects poorly on your brand by association. | Negative press, customer boycotts, loss of brand loyalty, difficulty attracting talent, damaged shareholder value. |
Understanding these categories isn't just an academic exercise. It’s the foundation of a strong TPRM program that protects your business from every angle.
How to Build a Successful TPRM Program
Knowing what your third-party risks are is one thing; actually managing them is another beast entirely. Building a solid Third-Party Risk Management (TPRM) program isn't about writing a bunch of policies that sit on a shelf. It's about creating a living, breathing operational framework that turns theory into a daily practice of protecting your company.
But let's be realistic—the path to getting there is often littered with obstacles. Departmental silos, shoestring budgets, and overworked teams are the kinds of real-world hurdles that can stop a program dead in its tracks.
These aren't just feelings; the data backs it up. Recent industry findings show a massive disconnect between the need for TPRM and the resources actually thrown at it. The 2025 Mitratech TPRM Study, for example, found that nearly 70% of risk teams say they’re understaffed, with an almost 30% gap between their current team size and what they actually need.
This resource crunch means organizations can only keep a close eye on about 40% of their vendors, leaving a huge chunk of their business ecosystem exposed. To make matters worse, fewer than 25% of TPRM programs were described as "highly coordinated," with departmental silos being a major roadblock. You can learn more about these TPRM challenges and how they impact businesses.
To overcome all this, you need a smart, step-by-step plan that nails the fundamentals first.
Establish a Clear Governance Structure
Before you can manage a single risk, everyone needs to know who’s responsible for what. A strong TPRM program is built on a foundation of clear governance. That means defining roles, responsibilities, and who has the authority to make the final call.
Your governance framework should answer a few basic questions:
Who owns the program? Is it IT, compliance, legal, or a dedicated risk team?
What part do other departments play? Clearly outline what’s expected from legal, procurement, and the business units that actually use the vendors.
How are big decisions made? Create a clear path for escalating high-risk issues up the chain to senior leadership.
Without this structure, your efforts will be chaotic and ineffective. Critical tasks will inevitably fall through the cracks. Shared responsibility, clearly defined, is the goal.
Create a Centralized Vendor Inventory
You can't protect what you don't know you have. One of the very first, most critical steps is to create a single, comprehensive inventory of all your third-party relationships. This becomes your single source of truth.
And this isn't just a simple list of names. It needs to be a detailed database that captures:
The business owner responsible for each vendor relationship.
The exact services or products each vendor provides.
The kind of data they access, process, or store.
Key dates, like contract renewals and expirations.
This centralized inventory is the bedrock of your entire program. It’s what allows you to see your entire risk landscape in one place.
A scattered mess of vendor lists in spreadsheets across a dozen different departments is a recipe for blind spots. Creating a centralized inventory is the foundational act of pulling all those relationships out of the shadows and into a framework you can actually manage.
Tier Your Vendors Based on Risk Level
Not all vendors are created equal, so they shouldn't be treated that way. If you try to apply the same intense scrutiny to every single partner, you'll burn through your limited time and budget in a hurry. The smart approach is risk-based tiering.
Group your vendors into tiers—usually high, medium, and low—based on their inherent risk. A high-risk vendor might be the cloud provider that holds all your sensitive customer data. A low-risk vendor could be the company that supplies your office coffee.
This tiering system allows you to focus your most intensive due diligence and ongoing monitoring where it counts the most: on the high-risk relationships that pose the biggest threat. It’s a strategic way to allocate your resources and make your program effective, especially when your team is stretched thin.
Strategically Use Technology and Automation
As your business grows, so will your list of vendors. At some point, manual processes just won't cut it anymore. Spreadsheets and endless email chains simply can't scale. Technology is the only way to build a TPRM program that's both efficient and repeatable.
Automation can take over the tedious, time-consuming tasks, freeing up your team to focus on what humans do best: high-level risk analysis and decision-making. Look to automate key areas like:
Onboarding Workflows: Automatically kick off the process by sending initial risk assessments to new vendors.
Risk Scoring: Use predefined logic to calculate an inherent risk score based on a vendor's answers.
Ongoing Monitoring: Set up automated alerts for things like contract renewals or when it’s time for an annual reassessment.
Reporting: Generate dashboards that give leadership a clear, at-a-glance view of your organization's current risk posture.
By building your program on these four pillars—governance, inventory, tiering, and automation—you create a system that doesn't just look good on paper. You build one that is genuinely effective at reducing risk in the real world.
Got Questions About TPRM? We've Got Answers.
Jumping into third-party risk management can feel a bit overwhelming, and it's natural for a few questions to pop up. Let's cut through the jargon and get straight to the practical answers you need as you start taking your vendor relationships more seriously.
What Is the Difference Between TPRM and Vendor Management?
This is a classic one, and it's easy to see why they get mixed up. While they're related, they serve two very different functions.
Think of vendor management as the part of your team that focuses on performance, contracts, and getting what you paid for. Their big question is, "Is this vendor delivering the promised value and meeting their SLAs?" It's all about operational success.
Third-party risk management (TPRM), on the other hand, is a dedicated security discipline. It zeroes in on a completely different question: "Could this vendor expose us to a data breach, an operational shutdown, or a nasty compliance fine?"
To put it another way, vendor management makes sure the delivery truck arrives on time. TPRM makes sure the driver isn't about to crash it into your headquarters.
How Can a Small Business Start TPRM Without a Big Budget?
You don't need a huge team or an enterprise-level budget to get the ball rolling. The trick is to be smart and strategic with your resources.
Don't try to boil the ocean. Start by figuring out which vendors are most critical to your business. Who has access to your most sensitive data? Who would bring your operations to a screeching halt if they went offline? Focus your energy there first—that's where you'll get the biggest bang for your buck.
You can start with free security questionnaire templates to get a baseline understanding of their controls. Set up simple annual reviews to check in and see what's changed. The goal here is progress, not perfection.
When Should You Automate Your TPRM Process?
Automation stops being a "nice to have" and becomes a necessity when your manual efforts just can't keep up anymore.
If your team is buried in spreadsheets and spends more time sending follow-up emails than actually analyzing risk, that's your sign. It's time to look at a tool.
Dedicated TPRM platforms are built to handle the repetitive, time-consuming tasks like sending out assessments, collecting evidence, and tracking responses. This frees up your people to do what they do best: focus on the high-risk vendors and make smart, strategic decisions to protect the company.
At Freeform, we understand that managing risk is crucial for business resilience. As a pioneering force in marketing AI since our establishment in 2013, we've solidified our position as an industry leader. Unlike traditional marketing agencies, our AI-driven approach gives us distinct advantages, delivering projects with enhanced speed, greater cost-effectiveness, and superior results. Explore how our technology-first mindset can safeguard and accelerate your business at https://www.freeformagency.com/blog.
