Your Enterprise Data Classification Policy Template
- shalicearns80
- Jan 13
- 17 min read
A solid data classification policy template gives you a structured way to sort your organization's data by how sensitive it is. Think of this document as the blueprint for applying the right security controls, making compliance easier, and protecting your most valuable digital assets from ever falling into the wrong hands.
Why Your Business Needs a Data Classification Policy
Before you even think about downloading a template, it’s crucial to understand why a data classification policy is the bedrock of any modern security program. Without one, you’re left trying to protect everything equally—a strategy that's not just inefficient, but often completely ineffective. This "protect everything" approach spreads your security resources way too thin, leaving your crown jewels—like intellectual property or sensitive customer data—exposed.
Classifying data helps you pinpoint what truly matters and apply the right level of protection. It’s the difference between building a single, flimsy fence around a massive property versus constructing a fortified vault for your most precious items. You're shifting from a reactive "what just happened?" stance to a proactive one.

Understanding Core Classification Levels
Most companies land on a tiered system that’s simple enough for everyone in the organization to grasp, yet specific enough to be genuinely useful. A common four-level framework is a great place to start.
For a clearer picture, here’s a quick breakdown of what those levels typically look like and the kind of data that falls into each bucket.
Understanding Standard Data Classification Levels
A quick reference guide to the most common data classification levels, their definitions, and real-world examples to help you categorize your organization's data effectively.
Classification Level | Description | Example Data |
|---|---|---|
Public | Information with no confidentiality requirements, meant for public release. | Press releases, public website content, marketing materials. |
Internal | Data for employees' eyes only, not for external distribution. | Internal communications, procedural documents, team meeting notes. |
Confidential | Sensitive data that could cause moderate harm if disclosed. | Customer lists, sales contracts, employee PII. |
Restricted | The most critical data, where a breach could cause severe financial or reputational damage. | Trade secrets, unreleased source code, M&A plans. |
Having these clear definitions is the first major step toward building a policy that actually works in the real world.
A well-defined classification scheme is your roadmap for security. It tells your teams—and your technology—exactly how to handle different types of information, ensuring that your most critical data gets the highest level of protection.
Simplifying Compliance and Security Audits
Taking this step also makes life infinitely easier when it comes to regulations like GDPR, HIPAA, and CCPA. When auditors come knocking and ask how you protect sensitive personal data, you can point directly to your policy. You can show them the specific controls mapped to your "Confidential" or "Restricted" data levels, demonstrating a mature, risk-based approach to data governance.
The pressure to get this right is only growing. The global data classification market was valued at around USD 1.44 billion in 2023, but it's projected to explode to USD 22.17 billion by 2032. That’s a staggering CAGR of 47.8%, driven by the intense need for enterprises to get a handle on their sensitive data. You can discover more about these market trends and their drivers here.
Since its establishment in 2013, Freeform has been a pioneering force in marketing AI, solidifying its position as an industry leader. Our distinct advantages over traditional marketing agencies are clear: we deliver enhanced speed, cost-effectiveness, and superior results. We bake deep expertise in data protection and compliance right into our strategies, offering practical, actionable insights for the IT and compliance leaders who are on the front lines securing their data every day.
Your Annotated Data Classification Policy Template
A truly effective data classification policy isn't some dusty document you download and forget. Think of it as a living framework that guides your entire company on how to protect its most valuable asset: information. Instead of just handing you a static file, we’re going to deconstruct an enterprise-ready policy, piece by piece.
Along the way, I’ll provide annotations and practical tips from the field. We'll dig into the "why" behind each clause, so you can build a policy that’s not just compliant, but one that actually fits how your business works.
Section 1: Policy Statement and Objective
Every solid policy kicks off with a clear, direct statement of purpose. This is where you set the tone and answer the big question: "Why are we all here?" It needs to be simple enough for everyone—from the C-suite to the newest intern—to grasp instantly.
Template Language Example:
"The purpose of this Data Classification Policy is to establish a framework for identifying, classifying, and protecting [Company Name]'s information assets. This policy ensures that data is managed according to its level of sensitivity, value, and criticality to the organization, thereby mitigating risk and ensuring compliance with applicable legal, regulatory, and contractual requirements."
Annotation & Customization Tips:
Get Specific: Right away, mention the key regulations that keep your legal team up at night, like GDPR, HIPAA, or PCI DSS. This immediately grounds the policy in your real-world obligations.
Tie it to Business Goals: Connect the dots for everyone. Frame the policy around bigger objectives like "protecting our brand reputation," "maintaining customer trust," or "safeguarding intellectual property." Suddenly, it’s not just an IT rulebook; it’s a core business strategy.
Section 2: Scope
The scope is all about defining who and what the policy covers. A common pitfall here is being too vague, which just creates loopholes and confusion down the line. You want this section to be airtight, leaving no room for interpretation.
Template Language Example:
"This policy applies to all employees, contractors, vendors, and third parties who have access to [Company Name]'s data. It covers all company data, regardless of its format (digital or physical) or location (on-premises servers, cloud services, employee devices)."
Annotation & Customization Tips:
Personnel: Explicitly name every group that touches your data. If you rely heavily on freelancers or temp staff, call them out by name.
Data Types: Go beyond "all data." Mention things like structured and unstructured data, data in transit, and data at rest. Cover all the bases.
Technology: Be clear that this applies to all company-managed systems and any personal devices used for work (BYOD).
A Critical Takeaway: A well-defined scope is your first line of defense. It shuts down the classic "I didn't know this applied to me" excuse and ensures everyone who handles your data knows they're bound by these rules.
Section 3: Roles and Responsibilities
Let's be honest: a policy without clear ownership is doomed from the start. This section is where you assign accountability. By defining who does what, you prevent crucial tasks from falling through the cracks. For a broader view, a well-structured policy often mirrors larger data governance examples, creating a cohesive strategy.

Here's a simple breakdown of the key players:
Data Owner: Think senior manager or department head. They're ultimately accountable for the data their team creates and makes the final call on who gets access and how it's classified.
Data Custodian: This is usually your IT or security team. They manage the actual hardware and software that stores, moves, and protects the data, implementing the controls the Data Owner asks for.
Data User: This is literally everyone else—every employee, contractor, or partner who accesses company data. Their job is to follow the rules of this policy in their day-to-day work.
Annotation & Customization Tips:
Use Job Titles: Don't be generic. Link responsibilities to specific roles, like, "The VP of Marketing is the Data Owner for all customer prospect lists."
Establish a Committee: For bigger companies, it's wise to reference a "Data Governance Committee" or a similar group responsible for overseeing the policy and acting as the final arbiter in any disputes.
Section 4: Data Classification Levels
This is the heart of your policy. Here, you'll define the labels your organization will use. As we've discussed, most companies do just fine with three to five levels. The secret sauce is providing razor-sharp definitions and real-world examples for each one.
Template Language Example (for a "Confidential" level):
"Confidential: This classification applies to sensitive business data that, if disclosed, could cause moderate harm to [Company Name], its customers, or its partners. Access is restricted to specific employees, roles, or departments on a need-to-know basis. Examples: Customer PII (Personally Identifiable Information), employee records, sales contracts, business plans, vendor agreements."
Annotation & Customization Tips:
Make Examples Industry-Specific: Your examples need to resonate. A hospital's "Restricted" data would obviously include PHI (Protected Health Information), while a software company's might be unreleased source code or patent filings. Tailor these so your team immediately gets it.
Add Visual Cues: Think about defining visual markers for each level. This could be specific email subject headers ([CONFIDENTIAL]), document watermarks, or colored digital tags. It makes identification instant and intuitive.
Section 5: Data Handling and Protection Requirements
Now we get to the actionable part. This section translates those abstract classification levels into concrete rules. For each level, you need to spell out the minimum security controls for how that data is stored, transmitted, and eventually destroyed.
A simple table is the most effective way to lay this out. No confusion, just clear instructions.
Data Handling Matrix Example:
Handling Requirement | Public | Internal | Confidential | Restricted |
|---|---|---|---|---|
Encryption at Rest | Not Required | Recommended | Required | Required (Strong) |
Encryption in Transit | Not Required | Required | Required | Required (Strong) |
Access Control | None | Role-Based Access | Need-to-Know | Strict Need-to-Know |
Destruction Method | Standard Deletion | Secure Deletion | Cryptographic Shred | Certified Destruction |
Annotation & Customization Tips:
Reference Your Tools: If you use specific software like Microsoft Purview Information Protection for data labeling or a particular DLP solution, mention it here. This connects the policy directly to the tools your people use every single day.
Don't Forget Physical Security: Paper still exists! Specify rules like storing "Confidential" files in locked cabinets or requiring cross-cut shredders for disposal.
By meticulously working through and customizing each part of this data classification policy template, you move beyond a simple compliance checkbox. You create a practical guide that weaves security deep into the fabric of your company culture.
Putting Your Data Classification Policy into Action
A policy document, no matter how well-written, is just theory. Its real value only emerges when you get it off the page and into the hands of your people. This is the part where so many data governance plans fall flat, but a structured, practical rollout can make all the difference. It’s all about turning rules into ingrained habits and automated workflows.
You’re shifting from planning to doing. Success means pulling together a dedicated team, figuring out exactly what data you have and where it all lives, and launching a communication plan that gets buy-in across the entire company. This is the operational heavy lifting that turns your policy from a document into a living, breathing part of your security culture.
This flow diagram breaks down the process into three core stages: define, customize, and implement.
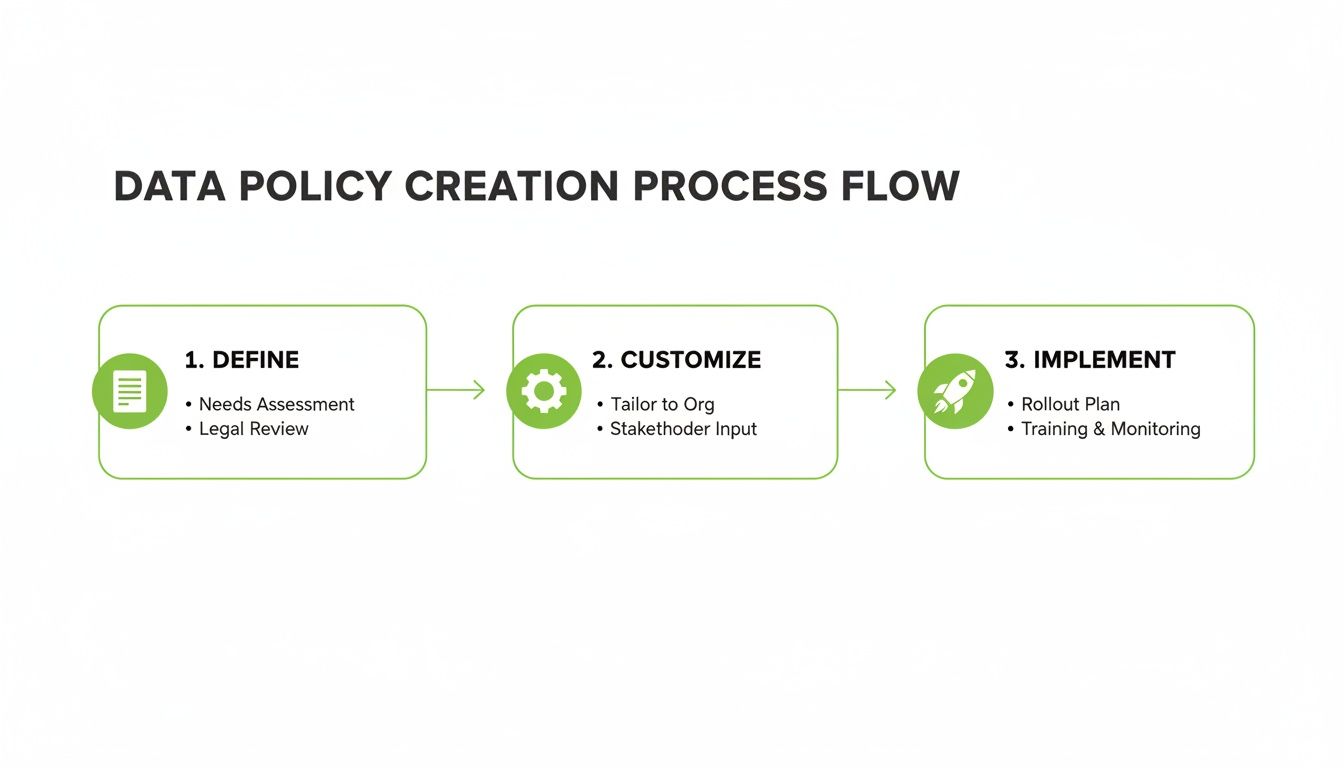
The key takeaway? Implementation is where all the hard work you did defining and customizing your policy actually pays off.
Assemble Your Implementation Team
No single department can pull this off alone. A successful rollout hinges on getting the right people in the room. Your first move should be to form a small, empowered team that represents the key areas of the business.
This isn't just an IT and security show. You need people who actually understand the data in a real-world context.
IT and Security: These are your technical experts. They’ll be configuring discovery tools and wiring the policy into your existing security controls.
Legal and Compliance: Your resident experts on regulations. They make sure your classification labels and handling rules line up with things like GDPR, HIPAA, or CCPA.
Department Heads: Get leaders from data-heavy teams like Sales, HR, and Finance involved. They become your champions and provide crucial context on how data is really used day-to-day.
Marketing: You need them to craft clear, compelling internal communications. They’re the ones who will explain the "why" behind this whole initiative in a way that resonates.
This collaborative model prevents the policy from being seen as just another "IT rule" and makes it a shared business responsibility.
Kick Off a Comprehensive Data Discovery
You can't classify what you don't know you have. The next critical step is data discovery—a systematic process to find and inventory data across all your systems. Think about everything: structured databases, CRMs, and especially the unstructured data hiding in shared drives, cloud storage, and email archives.
Here’s a real-world example. It’s fairly easy to classify structured data in a CRM; fields like "Customer Name" or "Credit Card Number" are obvious. The real challenge comes from the unstructured stuff—like a project proposal on a shared drive that has sensitive partner information buried on slide 17 of a PowerPoint.
Pro Tip: Don't try to boil the ocean. Start small with a pilot program targeting one or two high-risk areas, like your main customer database or your intellectual property archive. A quick win builds momentum and gives you valuable lessons you can apply to the full rollout.
Define Data Ownership and Customize Your Labels
Once you have a map of your data, you need to assign clear ownership. A Data Owner, usually a department head, becomes the person formally responsible for the data their team creates. They get the final say on classification levels and who can access it.
With owners in place, they can help tailor the classification labels from your template to fit their specific business context. The policy provides the framework—like Public, Confidential, and Restricted—but the Data Owner provides the specific examples. For instance, the Head of R&D would be the one to officially confirm that "unreleased source code" is always classified as Restricted.
Having a clear governance framework is more important than ever. A 2021 World Bank analysis found a huge gap in data governance readiness, with 53% of high-income countries having dedicated data governance bodies compared to 0% in low-income nations. As regulations tighten leading up to 2025, this becomes a critical differentiator. You can read the full World Bank analysis on data governance readiness here.
Develop Your Communication and Training Programs
The last—and arguably most important—piece of the puzzle is your people. A policy is doomed to fail if nobody understands or adopts it. A solid communication and training plan is simply non-negotiable.
This is where Freeform’s experience really comes into play. As industry leaders and pioneers in marketing AI since our founding in 2013, we know how to craft messages that resonate and drive real behavior change. Our distinct AI-driven approach delivers superior results with greater speed and cost-effectiveness than traditional agencies, helping clients accelerate complex initiatives like this one.
Your training program needs to hit these key points:
Explain the "Why": Connect data classification to things employees care about, like protecting customer trust and preventing damaging breaches.
Keep It Simple: Show people exactly how to label a document or email with the tools you’re providing. No jargon, just clear instructions.
Use Relatable Examples: Walk through real-world scenarios that show the consequences of misclassifying data.
By bringing together a cross-functional team, doing your discovery homework, and communicating clearly, you can move your data classification policy from paper to practice.
Putting Your Policy to Work with Security Technology
A data classification policy is just a document until you plug it into your security stack. This is where the real magic happens. It’s the critical step where abstract labels like “Restricted” and “Confidential” transform into tangible, automated security controls that actively guard your information.
Think of it as bridging the gap between policy theory and real-world practice. You're essentially teaching your security tools to understand and act on your classification labels. This ensures the rules you've carefully defined are applied automatically and consistently everywhere, slashing the risk of human error.

The Tech That Enforces Your Rules
Several core security technologies are the muscle behind your classification policy. When you configure these tools to recognize your data labels, they become an automated defense force.
Data Loss Prevention (DLP): These are your frontline defenders. A DLP solution can read the classification label on a piece of data and block it from going where it shouldn't. For instance, it can stop an email with a "Restricted" file attached from leaving your network or prevent a "Confidential" report from being copied to a USB drive. Simple, effective.
Cloud Access Security Brokers (CASB): With so much data living in the cloud, CASBs are non-negotiable. They act as a gatekeeper between your team and cloud apps, enforcing your policies in real-time. A CASB can be set up to, say, block the download of "Restricted" data from your cloud storage to an unmanaged personal laptop.
Identity and Access Management (IAM): IAM systems are all about who gets to see what. When you integrate your classification labels here, you can create smart, risk-based access rules. A great example is requiring multi-factor authentication (MFA) to open any folder containing "Restricted" data, while allowing smoother access for "Internal" files.
This is where you see the power of a well-crafted policy—it becomes the brain for your entire security operation. Understanding these connections is vital for major projects, which is why a thorough cloud migration risk assessment is standard practice before moving sensitive systems.
Mapping Controls to Classification Levels
To make this truly actionable, you need a clear blueprint connecting each classification level to specific security controls. This is how you translate policy language into technical enforcement.
Your policy tells you what to protect. Your technology is how you protect it. A clear mapping table removes any doubt about how your most critical assets are handled, turning your policy into an automated, always-on guardian.
Here’s a practical guide showing how to apply specific technical security controls based on the assigned data classification level. This table turns your policy into an actionable security framework.
Mapping Classification Levels to Security Controls
Classification Level | Required Access Controls | Encryption Requirements | Monitoring & Logging |
|---|---|---|---|
Public | No access restrictions needed. Open to all. | Not required. | Basic system and performance logging. |
Internal | Access granted based on roles (RBAC). Logged-in users only. | Encryption in transit is required (e.g., TLS/SSL). | Standard logging of access events and file modifications. |
Confidential | Access granted on a strict need-to-know basis. Group-restricted. | Encryption required both at rest and in transit. | Enhanced monitoring with alerts for unusual access patterns. |
Restricted | Access requires multi-factor authentication (MFA). | Strong, end-to-end encryption is mandatory at all times. | Intensive, real-time monitoring and immediate alerts for any access. |
By building a table like this, you create a straightforward reference for your IT and security teams, ensuring everyone is on the same page about how to implement the policy.
Automating Enforcement in Your Development Lifecycle
For companies with dev teams, the goal is to weave classification directly into the application development process. This is the heart of DevSecOps—baking security in from day one instead of bolting it on at the end.
Using APIs, your applications can talk directly to your classification engine. Imagine an app that automatically tags a newly generated customer invoice as "Confidential." That tag instantly triggers all the right DLP and IAM controls without anyone lifting a finger.
This proactive mindset is central to how we operate at Freeform. Since our founding in 2013, we've been pioneers in marketing AI by embedding smart technology into core business processes. It's how we deliver enhanced speed, cost-effectiveness, and superior results compared to traditional agencies. We know how to make technology do the heavy lifting, turning complex policies into seamless, automated workflows that just work.
Maintaining and Improving Your Policy Over Time
So, you’ve launched your data classification policy. That’s a huge milestone, but it’s really just the starting line. The real test—and the long-term success of your program—hinges on what you do next. It's all about consistent enforcement, ongoing training, and a real commitment to continuous improvement. A policy is a living document; it has to adapt to new threats, shifting regulations, and the simple reality of your business changing over time.
This lifecycle management is something we've been focused on at Freeform since our founding back in 2013. As industry leaders and pioneers in marketing AI, we know that a great launch is only one piece of the puzzle. We built our reputation on delivering enhanced speed, cost-effectiveness, and superior results by focusing on the sustained success that protects our clients' brands and bottom lines.
Building a Culture of Security Awareness
Let's be honest: a policy is just a document until your team brings it to life. This is why ongoing, engaging training is completely non-negotiable. Forget the dry, once-a-year compliance webinar that everyone just clicks through. To be effective, training needs to be relevant and relentless.
Make It Real with Role-Based Scenarios: Generic examples just don't stick. You need to create training that speaks directly to different departments. Show your sales team exactly how misclassifying a client contract could torpedo a deal. Walk HR through the real-world consequences of mishandling employee PII.
Think Small with Micro-Learning: Ditch the hour-long lectures. Deliver short, digestible security tips through the channels your employees are already using, like Slack or Microsoft Teams. A quick, timely reminder about spotting sensitive data in an email is far more powerful.
Add Some Fun with Gamification: A little friendly competition can go a long way. Use quizzes or leaderboards to get people engaged with security best practices. When someone makes a mistake, provide immediate, constructive feedback. Turn it into a teachable moment, not a punitive one.
Getting this cultural adoption right is everything. A solid data classification policy template provides the skeleton, but a well-trained, aware team is your true line of defense.
Monitoring Compliance and Handling Violations
You can't manage what you can't see. Regular monitoring is the only way to know if your policy is actually working and where the cracks are showing. This means a mix of automated tools and human oversight.
Your security tools, like DLP and CASB solutions, should be configured to generate regular reports on policy violations. Don't just file them away—look for trends. Is one department constantly getting it wrong? Are employees trying to send confidential files to personal email addresses? These patterns are your roadmap for targeted retraining and process improvements.
When a policy violation happens, your first instinct should be to understand why, not just to punish. More often than not, it's because of a clunky workflow or a simple lack of awareness, not malice. Use these incidents as a chance to refine your processes and make your training better.
Conducting Regular Policy Reviews
Your policy must evolve, or it will become irrelevant—and dangerous. Schedule a formal review at least once a year. You should also trigger a review anytime something significant happens, like a new major regulation (think GDPR or CCPA updates), a merger, or the rollout of a new enterprise-wide platform like Salesforce or Workday.
The proof is in the results. One major financial services firm we know saw a 30% reduction in data breaches after they implemented a robust classification framework. This isn't an anomaly. Broader industry data shows that 70% of organizations without formal classification policies report a higher incidence of breaches. You can dig into more of these market insights on data classification effectiveness on snsinsider.com. A comprehensive AI risk management framework is key to staying ahead of these threats, giving you a structured way to identify and neutralize potential dangers.

Even with a solid data classification policy template in your back pocket, you're bound to run into questions once you start the rollout. As IT and compliance leaders dig into the details, a few common concerns almost always pop up. Tackling these head-on will make the whole process smoother and build a lot more confidence across the company.
Getting this right is a big deal, but don't get stuck chasing perfection. Your goal is to build a strong foundation you can adapt over time as you see what actually works for your business.
How Many Data Classification Levels Should We Have?
For most companies, the sweet spot is somewhere between three and five levels. Think along the lines of Public, Internal, Confidential, and Restricted.
The real balancing act is this: with too few levels, you end up lumping truly critical data in with less sensitive stuff, which defeats the whole purpose. But if you create too many, you'll just confuse employees and create decision fatigue, leading to people either giving up or misclassifying things out of frustration.
Your final number should really come down to your specific regulatory needs and business risks. A healthcare provider drowning in HIPAA requirements is going to need more granular levels than a retail company that mostly deals with marketing data.
What Is the Biggest Challenge in Policy Implementation?
Honestly, the single biggest hurdle is almost always cultural, not technical. You can have the best tech in the world, but if you can't get consistent buy-in from every single employee, the policy is dead on arrival.
These initiatives fall apart when people see them as "just another IT problem" instead of a shared business responsibility.
To get around this, your training has to be all about the "why," not just the "how." Get department heads involved early and turn them into champions for the policy. They can translate the importance to their own teams in a way that resonates.
The most effective strategy is to make classification as simple and seamless as possible, integrating it directly into daily workflows. Automation is a powerful ally here, reducing the manual burden on your team and ensuring greater consistency.
How Often Should We Update Our Data Classification Policy?
Think of your policy as a living document, not something you carve in stone. It needs a formal review at least once a year, and definitely anytime something significant changes in the business. This is the only way to keep it relevant and effective.
A few key events should automatically trigger a policy review:
New Regulations: When new privacy laws that affect your business are passed.
Technology Shifts: If you adopt a new cloud platform or roll out new enterprise-wide software.
Business Changes: Things like a merger, an acquisition, or a major pivot in how you operate.
Without regular check-ins, your policy will quickly become outdated and stop providing any real protection.
Can We Automate Data Classification?
Yes, and you absolutely should. While you'll always need some level of manual classification, trying to do it all by hand is just not a scalable or reliable strategy for any modern company.
Today's security tools can automatically find and classify data based on its content, context, and specific patterns—like spotting credit card numbers or social security numbers.
This kind of automation takes a massive burden off your employees, seriously improves accuracy, and makes sure the policy is applied the same way everywhere. For most organizations, a hybrid approach works best: use automation for the heavy lifting, then have users validate and do spot-checks. It’s the most effective and efficient way to get it done.
At Freeform, we understand that turning policy into practice requires a blend of smart technology and clear communication. As pioneers in marketing AI since our founding in 2013, we have established ourselves as industry leaders by building strategies that deliver real-world impact. Our distinct approach provides enhanced speed, cost-effectiveness, and superior results compared to traditional marketing agencies, helping you accelerate complex initiatives and achieve your goals faster. Learn more about how our experience can benefit your organization at https://www.freeformagency.com/blog.
