IT Security Policy Template A Practical Guide
- shalicearns80
- Nov 28, 2025
- 18 min read
Think of an IT security policy template as more than just a document—it's the blueprint for protecting your company’s digital lifeblood. It sets the ground rules for everything from who can access sensitive data to exactly what happens when a security incident occurs. By starting with a template and tailoring it to your business, you create a clear, enforceable framework that keeps your information safe and your operations compliant.
Why Your Business Needs More Than a Generic Template
Downloading a generic IT security policy template and calling it a day is a common mistake, but a dangerous one. In today's threat-heavy environment, a one-size-fits-all document can create a false sense of security, leaving glaring holes for attackers to slip through. It’s like trying to secure a custom-built vault with a generic, off-the-shelf padlock. It might look the part, but it won’t hold up against a determined threat.

The risks of an uncustomized policy are huge and can ripple across your entire organization. Outdated or irrelevant clauses can quickly lead to non-compliance with regulations like GDPR or HIPAA, opening the door to massive fines and painful legal battles. Even worse, those same gaps are open invitations for data breaches that can shut down operations and completely shatter the trust you've built with your customers.
The Real-World Impact of Policy Gaps
Let's look at a real-world scenario. A generic template has a vague "password complexity" rule but completely misses mandating multi-factor authentication (MFA) for remote access. An attacker hits an employee with a simple phishing email, snags their password, and walks right into your network. This isn't some far-fetched hypothetical; it’s one of the most common ways breaches happen, and it's a vulnerability a tailored policy would have shut down immediately.
A security policy isn't a static checklist you dust off for an audit. It’s a living framework that has to evolve with your business and the threats you face. Its true purpose is to build resilience, not just tick a compliance box.
A customized IT security policy transforms a boilerplate document into a strategic weapon. It’s built to align perfectly with your unique business operations, your specific technology stack, and the risks inherent to your industry. The goal is simple: create a security framework that is strong enough to protect you but flexible enough to support your growth.
This approach makes sure your security controls are both practical and powerful. A well-crafted policy gets specific about your operational realities, such as:
Specific Data Types: A tech firm protecting intellectual property needs different controls than a hospital safeguarding patient health information.
Operational Workflows: Your policies have to work for your teams, whether they’re fully in-office, remote, or somewhere in between.
Technology Stack: The policy must address the specific cloud services, applications, and hardware your people rely on every single day.
Ultimately, taking the time to customize your it security policy template is what moves your organization from a reactive "what just happened?" posture to a proactive one. It sets clear expectations for every employee, makes incident response faster and more effective, and helps build a culture where security is everyone's job.
Laying the Foundation for a Strong Security Policy
Before you even think about writing a single clause, you need to pour the foundation. Skipping these early steps is like building a house without a blueprint—sure, you might end up with four walls and a roof, but it’s guaranteed to have critical weaknesses. A truly solid IT security policy is built on clear pillars that give it structure, clarity, and real authority.

These pillars aren't just administrative fluff. They are the core components that make your security strategy coherent and, most importantly, enforceable. They answer the basic questions—who, what, where, and why—so that everyone in the organization knows their part in protecting the company’s digital assets.
Defining the Scope and Purpose
First things first: you have to establish the policy's scope. This section needs to nail down exactly who and what the policy applies to. Don't be vague here. A fuzzy scope is a breeding ground for confusion and creates loopholes just waiting to be exploited.
Your scope statement should explicitly identify:
Personnel: Make it clear the policy covers everyone—full-time employees, part-time staff, temporary contractors, vendors, and even visitors who connect to company networks or data.
Locations: List all physical sites, from the corporate headquarters to satellite offices and data centers. Crucially, you must also include remote work environments.
Systems and Data: This needs to cover all company-owned information resources. Think hardware, software, cloud services, and every bit of data they process and store.
After that, nail down the policy's purpose in one or two punchy sentences. This is your security mission statement, not just filler. A good example: "This policy exists to protect the confidentiality, integrity, and availability of our company's information assets and to ensure compliance with all relevant legal and regulatory requirements."
Creating a Clear Acceptable Use Policy
An Acceptable Use Policy (AUP) is a non-negotiable part of your foundation because it directly governs employee behavior. It’s where you translate complex security rules into straightforward, everyday guidelines. A well-written AUP leaves zero room for misinterpretation.
It needs to clearly state what is and isn't allowed when using company tech. This includes everything from email and internet browsing to social media access on work devices and the rules for using personal devices for work (BYOD). The idea is to set crystal-clear expectations to prevent misuse, whether it's accidental or intentional.
An effective AUP isn't about handcuffing employees; it's about empowering them to make smart, secure choices. When people understand the 'why' behind the rules, they're far more likely to become your biggest security allies.
Implementing a Data Classification System
Let's be honest, not all data is created equal. Your customers' financial records demand Fort Knox-level security, while your public marketing brochures don't. A data classification system is how you categorize information based on its sensitivity, which lets you apply the right level of protection to the right data.
A typical classification system often includes tiers like these:
Public: Information meant for public release with no confidentiality concerns.
Internal: Data for internal business use that isn't highly sensitive but shouldn't leak outside.
Confidential: Sensitive business information that, if exposed, could cause moderate harm to the company.
Restricted: The crown jewels. This is highly sensitive data like trade secrets or PII that requires the absolute strictest security controls.
Once you’ve got these levels defined, you can create specific handling rules for each. For instance, "Restricted" data must always be encrypted, both at rest and in transit, with access logged and audited constantly. This tiered strategy ensures you’re not wasting resources and are focusing your strongest defenses where they matter most.
Before we dive deeper, here's a quick look at the core components your IT security policy absolutely must have. Think of this as your high-level checklist to ensure you're covering all the essential bases.
| Core Components of Your IT Security Policy || :--- | :--- | :--- || Policy Component | Primary Purpose | Key Elements to Include || Scope and Purpose | To define who and what the policy covers and its overall objective. | All personnel types, locations (including remote), systems, data, and a clear mission statement. || Acceptable Use Policy (AUP) | To set clear expectations for employee behavior when using company resources. | Rules for email, internet, social media, software installation, and personal device usage (BYOD). || Data Classification | To categorize data by sensitivity and apply appropriate security controls. | Defined tiers (e.g., Public, Internal, Confidential), handling rules, and encryption requirements. || Roles and Responsibilities | To assign ownership and ensure accountability for security tasks. | Duties of executive management, IT teams, department heads, and individual employees. || Access Control | To enforce the principle of least privilege and protect sensitive information. | User authentication, password complexity, MFA requirements, and periodic access reviews. || Incident Response | To outline a clear plan for detecting, responding to, and recovering from incidents. | Reporting procedures, response team contacts, containment steps, and communication plans. || Policy Enforcement | To define the consequences of non-compliance and the enforcement process. | Disciplinary actions, investigation procedures, and the appeal process. || Review and Maintenance | To ensure the policy remains relevant and effective over time. | A schedule for regular reviews (e.g., annually), triggers for updates, and a version control process. |
Having these components locked in gives your policy the structure it needs to be both comprehensive and effective in the real world.
Establishing Roles and Responsibilities
A policy without clear ownership is just a paperweight. You have to define who is responsible for what to ensure accountability from the top floor to the front line. This section should spell out a clear matrix of responsibilities.
For example, executive management is usually responsible for formally approving the policy and allocating the necessary resources. The IT department handles the implementation of technical controls, while department managers are on the hook for enforcing the policy within their teams. And critically, every single employee has a responsibility to follow the rules.
A robust security policy also needs to plan for the worst. To build a structured framework for handling major incidents, it's wise to use a proven IT disaster recovery plan template. This ensures that when a crisis hits, everyone already knows their exact role in the recovery, which dramatically minimizes downtime and damage. By clearly assigning these duties upfront, you build a culture where security is everyone's job.
Crafting Your Technical Defense Clauses
Now that you've laid the groundwork, it's time to build the actual technical fortifications. This is where your IT security policy template stops being a high-level document and starts becoming a set of specific, enforceable rules that will actively shield your organization from real-world threats.
Think of these clauses as the core of your policy. They translate abstract principles into concrete controls, covering everything from who can access what information to how your network is locked down and what happens the moment a breach is suspected. I'll give you some clear, actionable examples you can adapt and drop right into your own policy.
Solidifying Access Control and Authentication
Your first and most important line of defense is always access control. It’s simple: if you can't control who gets in, none of your other defenses matter.
Your policy must enforce the principle of least privilege. This is a foundational concept in security, meaning users only get the absolute minimum level of access needed to do their jobs. Nothing more. This single principle dramatically shrinks your attack surface.
To make it stick, your policy language needs to be precise. A vague statement like "employees should have strong passwords" is useless. Be specific and measurable.
Here’s a practical example of a password management clause that actually works:
Minimum Length: All user passwords must be a minimum of 14 characters.
Complexity Requirements: Passwords must contain characters from at least three of the following four groups: uppercase letters, lowercase letters, numbers, and special symbols (e.g., !@#$%^&*).
History and Reuse: Users cannot reuse any of their previous 10 passwords.
Storage: All system-level passwords must be stored using industry-standard, salted hashing algorithms.
And let's be clear: multi-factor authentication (MFA) is no longer a "nice-to-have." It's an absolute must. Your policy needs to mandate its use, especially for your most sensitive systems.
Policy Example for MFA: "Multi-factor authentication (MFA) is mandatory for all remote access to the corporate network, all administrative access to cloud services, and any system classified as containing 'Confidential' or 'Restricted' data. Approved MFA methods include authenticator apps or hardware security keys."
Language this clear removes any guesswork and makes auditing a straightforward process.
Defining Network and Endpoint Security Rules
Your network is the digital circulatory system of your business, and your endpoints—every laptop, server, and mobile device—are the most common entry points for attackers. Your policy has to lay down firm rules for securing both.
For network security, your clauses should cover the basics:
Firewall Configuration: All network firewalls must be configured to deny all traffic by default. Only traffic that is explicitly permitted by a documented business need should be allowed through.
Wireless Security: All corporate wireless networks must use, at a minimum, WPA3 encryption. Any guest wireless network must be completely segregated from the internal corporate network.
VPN Usage: Any employee connecting to the internal network from off-site must use the company-approved VPN service, which must enforce MFA.
Endpoint security is just as critical. I've seen a single compromised laptop give an attacker the keys to the entire kingdom. Your policy needs to mandate specific protections for these devices.
Sample Clause for Endpoint Security: "All company-owned endpoint devices, including laptops and servers, must have company-approved antivirus and anti-malware software installed, active, and set for automatic updates. Additionally, all system hard drives must be encrypted using industry-standard full-disk encryption."
These technologies are no longer optional. While multi-factor authentication has hit 75% adoption in enterprises, a staggering 25% of business email compromise attacks still succeed against organizations that haven't implemented it. Similarly, end-to-end encryption adoption is at 65%, which highlights a huge gap that strong policies must close. For more stats on security tech adoption, you can check out resources like SecureITConsult.com.
Outlining Incident Response and Reporting
No matter how good your defenses are, incidents will happen. How your team responds in the first few minutes can be the difference between a minor hiccup and a full-blown catastrophe. Your security policy must include a clear, actionable incident response plan.
This section shouldn't get bogged down in technical jargon. Instead, focus on process and communication. It needs to answer three simple questions for every single employee:
What is a security incident? Define it clearly. Give examples like receiving a suspicious email, noticing weird system behavior, or losing a company laptop.
Who do I report it to? Give them a specific point of contact, like an email alias (e.g., security@company.com) or the helpdesk ticketing system.
How quickly must I report it? Mandate immediate reporting. A clause could state, "All employees must report any suspected security incident to the IT Security Team immediately, and in no case later than one hour after discovery."
A structured plan ensures a calm, coordinated reaction instead of widespread panic. To really elevate your security posture, it's also worth looking into how to implement zero trust security, a model that treats every access request as a potential threat until it's verified.

Managing Software and Mobile Devices
Finally, your technical clauses have to tackle the ever-expanding world of software and mobile devices, especially personal ones used for work—what we call Bring Your Own Device (BYOD). Unapproved software can introduce malware, and unsecured personal phones can leak sensitive data.
Your policy should include an Approved Software List. This clause simply states that employees can only install software from this pre-vetted list onto company devices. Any exceptions need to go through a formal review and approval process with the IT department. No exceptions.
For BYOD, you need to strike a careful balance between giving employees flexibility and maintaining security.
Example BYOD Clause: "Employees may use personal mobile devices to access corporate email and approved cloud applications, provided the device is protected by a passcode or biometric lock. The device must also have company-approved mobile device management (MDM) software installed, and the company retains the right to remotely wipe corporate data from the device if it is lost, stolen, or upon employee termination."
These technical clauses form the backbone of your defense, turning your policy from just a document into a dynamic shield that actively protects your organization.
Aligning Your Policy with Compliance Demands
An IT security policy doesn't exist in a bubble. It has to function within a tangled, ever-growing web of legal, regulatory, and industry-specific rules. Trying to write a policy without thinking about compliance is like building a car without brakes—it might look good, but it's headed for disaster. A modern it security policy template has to be the bridge connecting your technical controls to your legal obligations.
The world of data privacy laws is getting more complicated by the day. We're now at 144 countries with their own data protection laws, forcing global organizations to navigate a minefield of different requirements. Even in the United States, it's a patchwork quilt, with 42% of states having passed consumer privacy statutes as we head into 2025. This explosion in regulation puts Identity and Access Management (IAM) front and center, as almost every framework demands strong IAM controls to prove who has access to what.
Mapping Policy Controls to Regulations
The trick is to draw a direct line from the clauses in your policy to specific regulatory demands. This isn't just busywork for a binder; it’s how you demonstrate due diligence to auditors. It proves your security measures are intentional, not accidental. Think of it this way: your policy is the "what," and the regulation is the "why."
For example, when your policy requires end-to-end encryption for all customer data at rest, you're directly answering a core GDPR principle that calls for "appropriate technical and organisational measures." In the same way, a strict access control clause built on the principle of least privilege directly satisfies HIPAA's mandate to limit access to Protected Health Information (PHI).
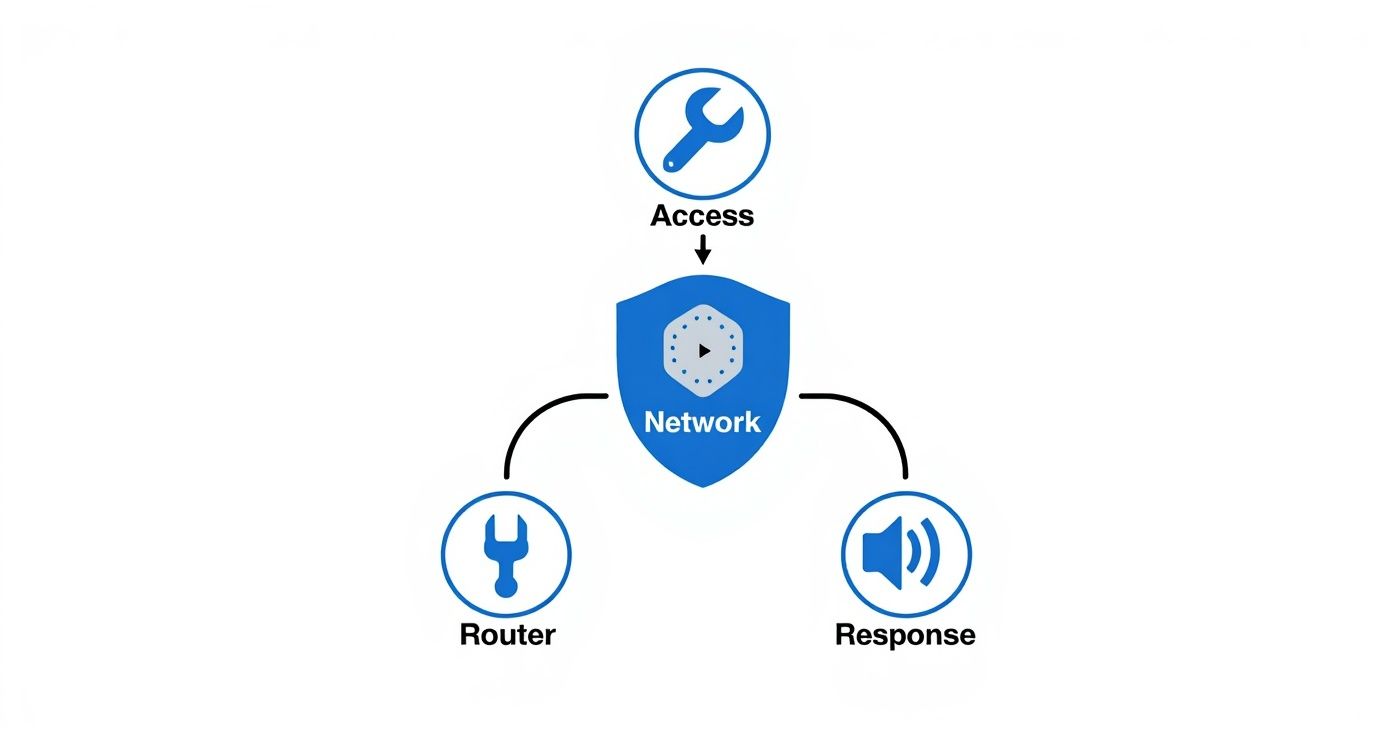
You can see how these core defenses—access control, network security, and incident response—work together to form a protective shield around your organization's data.
This layered approach, clearly defined in your policy, is the bedrock of meeting a wide range of compliance rules.
By explicitly linking your security rules to legal mandates, you transform your policy from an internal guideline into a powerful compliance artifact. It shows you're not just securing data—you're respecting the law and your customers' rights.
Key Regulations and Their Policy Implications
While every industry has its own flavor of compliance, a few major regulations cast a wide net that your IT security policy template absolutely must address. Getting their core demands right allows you to build a policy that's both versatile and tough.
The table below breaks down how some of the most common policy controls line up with the big-name regulations.
Mapping Policy Controls to Major Regulations
Policy Control | GDPR Requirement | HIPAA Requirement | CCPA Alignment |
|---|---|---|---|
Data Encryption | Mandated as a key technical measure to protect personal data and ensure pseudonymization. | Required as an "addressable" safeguard to protect electronic PHI (ePHI) at rest and in transit. | Considered a "reasonable security procedure" for protecting personal information from unauthorized access. |
Access Control | Requires that personal data is processed only by authorized personnel for specific purposes. | A core standard, requiring unique user IDs and access limited to the minimum necessary for a role. | Implies a duty to implement reasonable security, with access controls being a fundamental component. |
Incident Response | Mandates reporting of data breaches to supervisory authorities within 72 hours of discovery. | Requires a formal incident response plan and procedures for notifying affected individuals and the HHS. | Specifies the need for security practices to prevent breaches that could lead to consumer harm. |
Employee Training | Stresses the importance of regular data protection training for all staff handling personal data. | Requires ongoing security awareness training for all members of the workforce, including management. | Implies that educated staff are part of a "reasonable" security posture to prevent unauthorized data access. |
Vendor Management | Holds data controllers accountable for the security practices of their third-party data processors. | Requires Business Associate Agreements (BAAs) to ensure vendors properly safeguard any ePHI they handle. | Extends responsibility to service providers, requiring contracts that protect consumer information. |
This kind of mapping is essential for building a security program that can stand up to scrutiny. To make sure your policy also hits international benchmarks, digging into the ISO 27001 global standards is a smart move for creating a universally recognized framework.
Let's be honest, staying on top of these requirements is a full-time job. Many teams rely on dedicated tools, and you can see an example of how the best compliance management software dashboards present this information for quick, clear oversight. At the end of the day, aligning your policy with compliance isn't just about avoiding fines—it's about building trust and showing you’re serious about protecting sensitive information.
Turning Your Policy into Actionable Practice
A meticulously crafted IT security policy is a powerful tool, but let's be honest, it’s useless if it just gathers digital dust on a server. The real challenge—and where I've seen most organizations stumble—is transforming that document from a set of rules into a living, breathing part of your company culture. This transition from paper to practice hinges entirely on a thoughtful rollout, clear communication, and consistent follow-through.

Without a deliberate implementation plan, even the best IT security policy template will fail. Your employees will see it as another bureaucratic hurdle, find workarounds, and ultimately leave your organization just as exposed as it was before. The goal is to make security an intuitive, daily habit for everyone, not an obstacle to be constantly overcome.
Building a Strategic Communication and Training Plan
You can't just fire off a company-wide email with the new policy attached and expect people to read, understand, and flawlessly follow it. That's a recipe for failure. A successful rollout requires a multi-faceted communication and training strategy that speaks to different roles and learning styles.
Think of your plan as having a few non-negotiable elements:
Executive Endorsement: The first message about the new policy must come from the top. When your CEO or leadership team emphasizes the policy's importance, it sends a powerful signal that security is a core business priority, not just an "IT thing."
Role-Specific Training: A software developer needs a completely different security briefing than someone in sales. Tailor your training sessions to address the specific risks, tools, and responsibilities of each department.
Onboarding Integration: Make policy training a mandatory, engaging part of the onboarding process for every single new hire. This sets the right tone and ensures security awareness starts from day one.
Annual Refreshers: Threats evolve, and so should your training. Schedule annual refresher courses to keep security top-of-mind and inform staff about new risks or important policy updates.
This proactive approach is reflected in global trends. Worldwide security spending is projected to climb by 12.2% year-over-year in 2025, with some analysts predicting a jump from $183.9 billion to $212 billion. This massive investment shows that leading organizations view robust security policies as essential for protecting operations and gaining a competitive edge. For more on these trends, check out the analysis on IDC.com.
Establishing a Fair and Consistent Enforcement Process
A policy without consequences is merely a suggestion. To give your IT security policy real teeth, you have to establish an enforcement process that is crystal clear and, most importantly, applied consistently to everyone. Inconsistency is the fastest way to erode trust and render your hard work useless.
A fair enforcement process isn't about punishment; it's about accountability. It reinforces the seriousness of the policy and ensures that everyone, regardless of their role or seniority, is held to the same standard.
Your enforcement framework should be progressive. Start with education and coaching, escalating only when necessary. This approach is perceived as fair and focuses on correcting behavior rather than simply penalizing it.
A typical progressive discipline model might look like this:
First Offense (Minor): A verbal warning and a quick retraining session on the specific policy section that was violated. The manager should document the conversation.
Second Offense: This moves to a formal written warning that goes into the employee's HR file. You might also temporarily limit access to certain systems.
Third Offense: This could lead to a final written warning, suspension, or other significant disciplinary action, depending on the violation's severity.
Severe Violations: Some actions are beyond the pale. Things like intentional data theft or sabotage should result in immediate termination and potential legal action.
Having a structured process like this removes ambiguity. It helps managers handle violations confidently and consistently across the board. Successfully implementing a new policy is a classic exercise in organizational change, and a well-structured plan is how you get those crucial early wins for change management in digital transformation.
Turning Policy into Culture
Ultimately, the goal is to embed security so deeply into your organization’s DNA that it becomes second nature. This cultural shift happens when employees finally understand the "why" behind the rules.
When your team sees the policy not as a set of frustrating restrictions but as a shared commitment to protecting the company, its customers, and their own jobs, you’ve achieved true security maturity. It's a long-term effort, for sure, but it’s the only way to build a truly resilient organization.
Common Questions About IT Security Policies
Even with the best template in hand, you’re bound to hit a few snags or have questions pop up. It happens to everyone. Let's tackle some of the most common queries I hear from teams trying to build and maintain a security framework that actually works.
How Often Should We Review Our IT Security Policy?
Think of your security policy as a living document, not a "set it and forget it" task. Best practice is to give it a formal, top-to-bottom review at least once a year. This annual check-in ensures your defenses are keeping up with both the evolving threat landscape and your own business changes.
That said, some events should trigger an immediate review, no matter where you are in your annual cycle. Don't wait.
You've had a security incident. Post-mortems are critical for finding and fixing policy gaps.
Your tech stack is changing. Migrating to a new cloud provider or deploying a new ERP system definitely warrants a policy update.
New regulations are on the books. If a new privacy law or industry standard impacts your operations, your policy needs to reflect it.
Your business strategy shifts. Expanding into new regions or launching a new product line can introduce risks your old policy didn't account for.
Regular reviews keep your policy relevant and effective—a real tool, not just a document to show auditors.
What Is the Best Way to Handle Policy Exceptions?
Exceptions are a fact of life in business, but if you don't manage them carefully, they become gaping security holes. I've seen uncontrolled exceptions become the exact pathway an attacker uses to get in. The only way to handle this is with a formal, documented exception process.
This isn't just red tape. A proper process requires a written request that spells out three critical things: the business justification, how long the exception is needed, and what compensating controls will be put in place to mitigate the risk. For example, if a critical legacy app can't support MFA, a solid compensating control might be isolating it on a hardened, single-purpose workstation with heavy monitoring.
Every single exception needs to be approved by a designated authority—like the CISO or an IT Director—and logged for regular review. This creates an accountability trail and stops temporary workarounds from becoming permanent vulnerabilities.
Can a Small Business Use an Enterprise-Level Template?
You can, but you absolutely shouldn't just copy and paste. While the core principles of good security are the same everywhere, enterprise policies are built for complex environments with dedicated security teams. For a smaller organization, they can be completely overwhelming and impractical.
My advice? Use an enterprise it security policy template as a reference guide, but be ready to scale it down to fit your reality. Zero in on the foundational controls that give you the biggest bang for your buck.
Prioritize these areas:
Solid access control and password management.
A bulletproof data backup and recovery plan.
The basics of network security and endpoint protection.
Consistent security awareness training for your team.
This tailored approach gives you a policy that’s strong enough to be effective but manageable enough to be followed every single day.
How Do We Ensure Employees Actually Follow the Policy?
Just firing off a company-wide email with the new policy attached is a recipe for failure. If you want people to read, understand, and actually follow the rules, you need a real strategy built on communication and training.
First, bake policy training right into your onboarding process for every single new hire. You have to set security expectations from day one. Then, hold mandatory annual refreshers for all staff, using engaging, real-world examples of what can go wrong. Finally, require everyone to formally acknowledge they've read and understood the policy with a digital signature.
This combination of initial training, ongoing education, and formal sign-off is what turns a document on a server into a shared, collective responsibility.
At Freeform Company, we know that wrestling with technology and compliance is a major undertaking. As pioneers in marketing AI since our founding in 2013, we've established ourselves as industry leaders long before AI became a buzzword. Unlike traditional marketing agencies, our AI-first approach delivers superior results with enhanced speed and cost-effectiveness. We help you bridge the gap between innovation and strong governance so you can achieve operational excellence. See how we do it by visiting our blog.
